-
Infection repeatedly adds scheduled tasks and increases traffic to the same C2 domain, (Wed, Jan 14th)
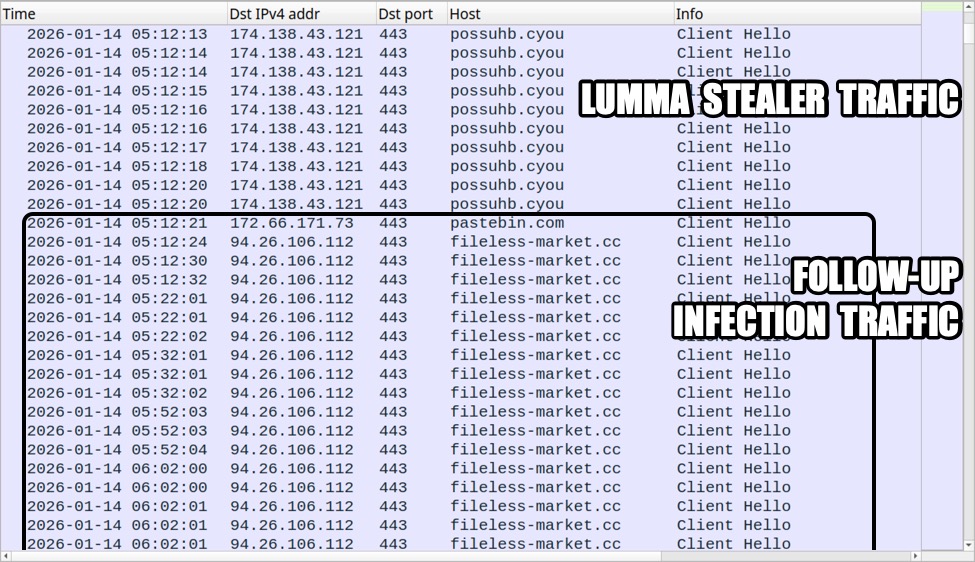
Introduction In recent weeks, Lumma Stealer infections have followed a specific pattern in follow-up activity. This pattern adds scheduled tasks for the same action, which increases traffic to the same C2 domain. This diary documents an example from one of these infections on January 14, 2026. Details After Lumma Stealer performs its data exfiltration, the…
-
ISC Stormcast For Wednesday, January 14th, 2026 https://isc.sans.edu/podcastdetail/9766, (Wed, Jan 14th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
January 2026 Microsoft Patch Tuesday Summary, (Tue, Jan 13th)
Today, Microsoft released patches for 113 vulnerabilities. One of these vulnerabilities affected the Edge browser and was patched upstream by Chromium. Eight of the vulnerabilities are rated critical. One has been disclosed before today, and one is already being exploited. Five of the critical vulnerabilities affect Microsoft Office components. Noteworthy Vulnerabilities %%cve:2026-20854%%: A remote code…
-
ISC Stormcast For Tuesday, January 13th, 2026 https://isc.sans.edu/podcastdetail/9764, (Tue, Jan 13th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Monday, January 12th, 2026 https://isc.sans.edu/podcastdetail/9762, (Mon, Jan 12th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
YARA-X 1.11.0 Release: Hash Function Warnings, (Sun, Jan 11th)
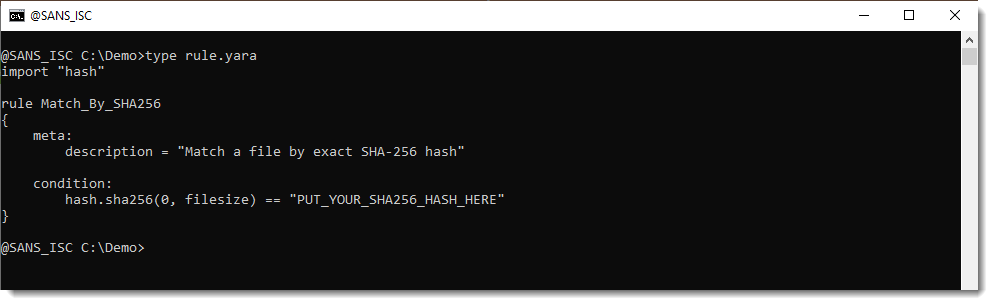
YARA-X’s 1.11.0 release brings a new feature: hash function warnings. When you write a YARA rule to match a cryptographic hash (either the full file content or a part of it), what’s actually going on are string comparisons: Function hash.sha256 returns a string (the hexadecimal SHA256 hash it calculated) and that is compared to a…
-
Malicious Process Environment Block Manipulation, (Fri, Jan 9th)
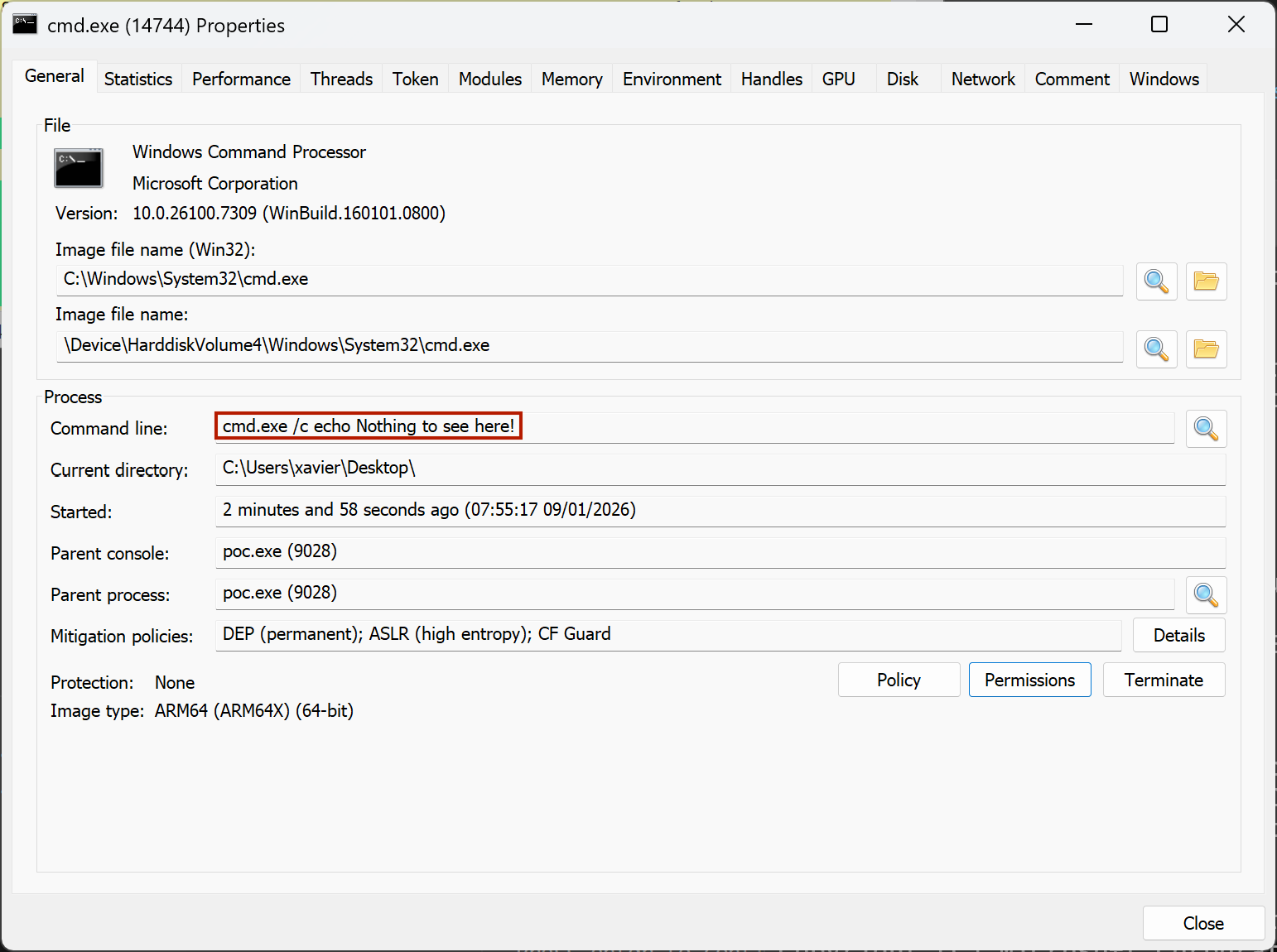
Reverse engineers must have a good understanding of the environment where malware are executed (read: the operating system). In a previous diary, I talked about malicious code that could be executed when loading a DLL[1]. Today, I’ll show you how a malware can hide suspicious information related to created processes. The API call CreateProcess() is…
-
ISC Stormcast For Friday, January 9th, 2026 https://isc.sans.edu/podcastdetail/9760, (Fri, Jan 9th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Thursday, January 8th, 2026 https://isc.sans.edu/podcastdetail/9758, (Thu, Jan 8th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Analysis using Gephi with DShield Sensor Data, (Wed, Jan 7th)
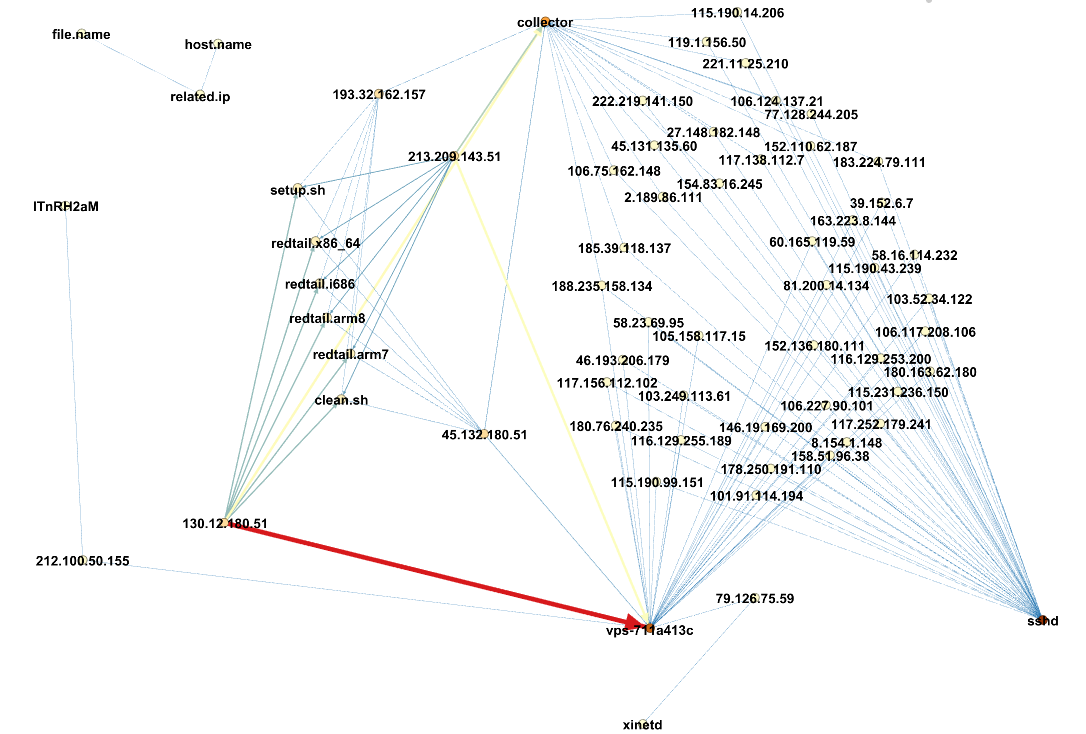
I’m always looking for new ways of manipulating the data captured by my DShield sensor [1]. This time I used Gephi [2] and Graphiz [3] a popular and powerful tool for visualizing and exploring relationships between nodes, to examine the relationship between the source IP, filename and which sensor got a copy of the file.…

