-
Automatic Script Execution In Visual Studio Code, (Wed, Jan 21st)
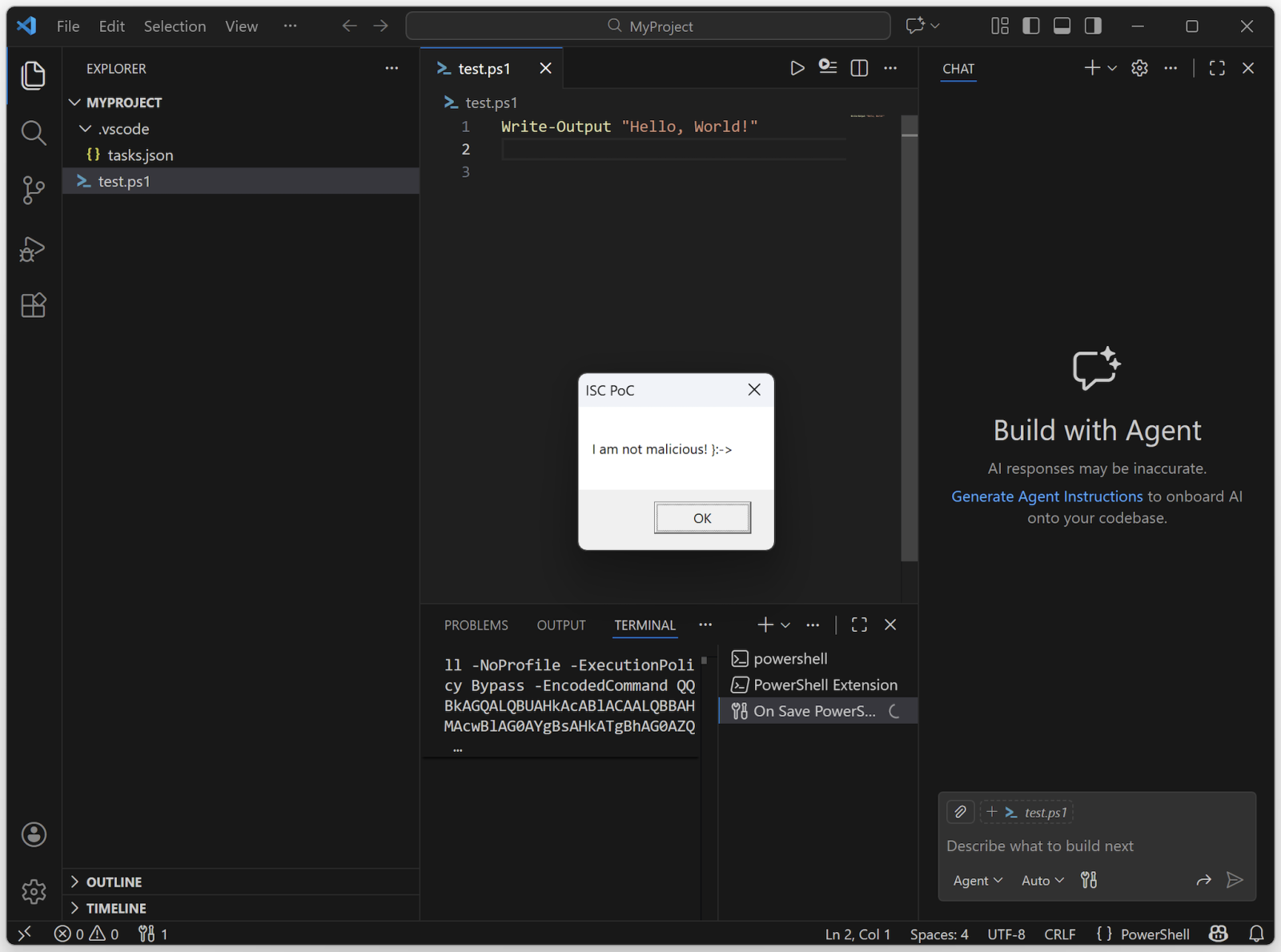
Visual Studio Code is a popular open-source code editor[1]. But it’s much more than a simple editor, it’s a complete development platform that supports many languages and it is available on multiple platforms. Used by developers worldwide, it’s a juicy target for threat actors because it can be extended with extensions. Of course, it became a…
-
ISC Stormcast For Wednesday, January 21st, 2026 https://isc.sans.edu/podcastdetail/9774, (Wed, Jan 21st)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Add Punycode to your Threat Hunting Routine, (Tue, Jan 20th)
IDNs or “International Domain Names” have been with us for a while now (see RFC3490[1]). They are (ab)used in many attack scenarios because.. it works! Who can immediately spot the difference between: https://youtube.com/ And: https://youtube.com/ The magic is to replace classic characters by others that look almost the same. In the example above, the letter “o”…
-
ISC Stormcast For Tuesday, January 20th, 2026 https://isc.sans.edu/podcastdetail/9772, (Tue, Jan 20th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
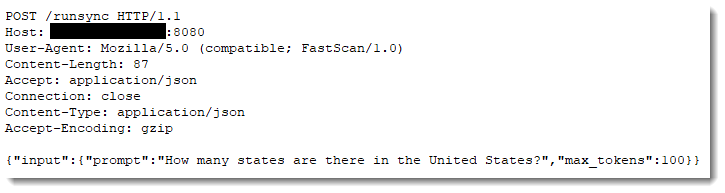
“How many states are there in the United States?”, (Sun, Jan 18th)
I’ve seen many API requests for different LLMs in the honeypot logs. Like this one: The prompt is always the same: “How many states are there in the United States?”. This is recon to find open LLMs. Not necessarily to exploit them, but to use them. Coincidentally, something similar has been reported in the news: “Hackers…
-
Wireshark 4.6.3 Released, (Sat, Jan 17th)
Wireshark release 4.6.3 fixes 4 vulnerabilities and 9 bugs. Didier Stevens Senior handler blog.DidierStevens.com (c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Friday, January 16th, 2026 https://isc.sans.edu/podcastdetail/9770, (Fri, Jan 16th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
![Battling Cryptojacking, Botnets, and IABs [Guest Diary], (Thu, Jan 15th)](/wp-content/uploads/2026/01/Matthew_Presnal_pic1-YPekwU.png)
Battling Cryptojacking, Botnets, and IABs [Guest Diary], (Thu, Jan 15th)
[This is a Guest Diary by Matthew Presnal, an ISC intern as part of the SANS.edu BACS program] Cryptojacking and botnets can pose a greater threat than a simple drain of resources. These organizations have been known to engage in “DDoS for Hire” or even selling off footholds, acting as Initial Access Brokers (IABs). To…
-
ISC Stormcast For Thursday, January 15th, 2026 https://isc.sans.edu/podcastdetail/9768, (Thu, Jan 15th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
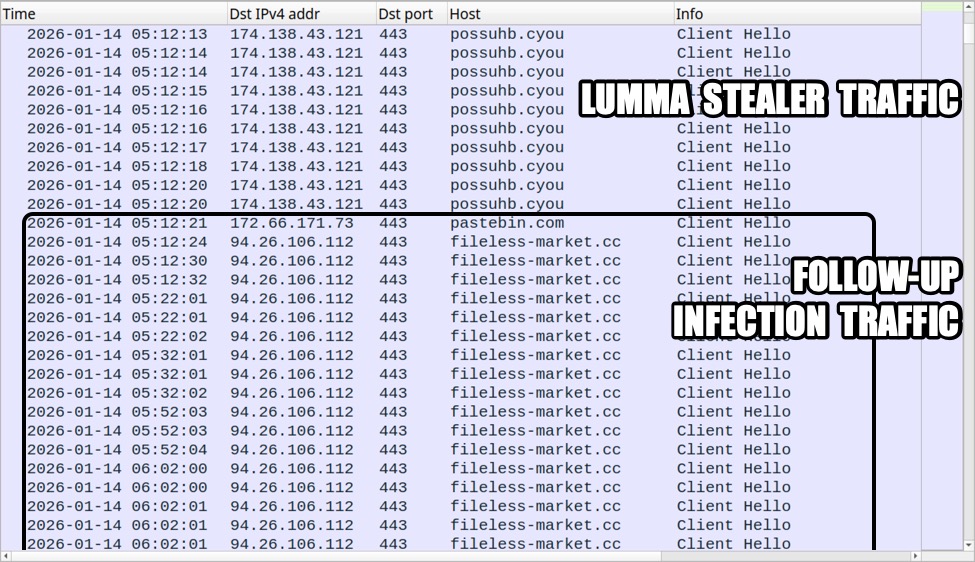
Infection repeatedly adds scheduled tasks and increases traffic to the same C2 domain, (Wed, Jan 14th)
Introduction In recent weeks, Lumma Stealer infections have followed a specific pattern in follow-up activity. This pattern adds scheduled tasks for the same action, which increases traffic to the same C2 domain. This diary documents an example from one of these infections on January 14, 2026. Details After Lumma Stealer performs its data exfiltration, the…

