-
Formbook Delivered Through Multiple Scripts, (Thu, Nov 13th)
When I’m teachning FOR610[1], I always say to my students that reverse engineering does not only apply to “executable files” (read: PE or ELF files). Most of the time, the infection path involves many stages to defeat the Security Analyst or security controls. Here is an example that I found yesterday. An email was received…
-
ISC Stormcast For Thursday, November 13th, 2025 https://isc.sans.edu/podcastdetail/9698, (Thu, Nov 13th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
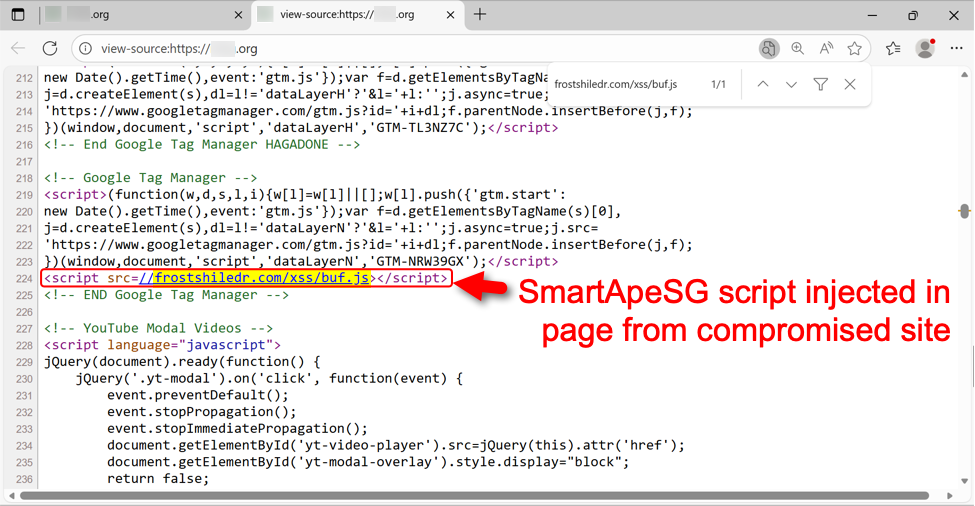
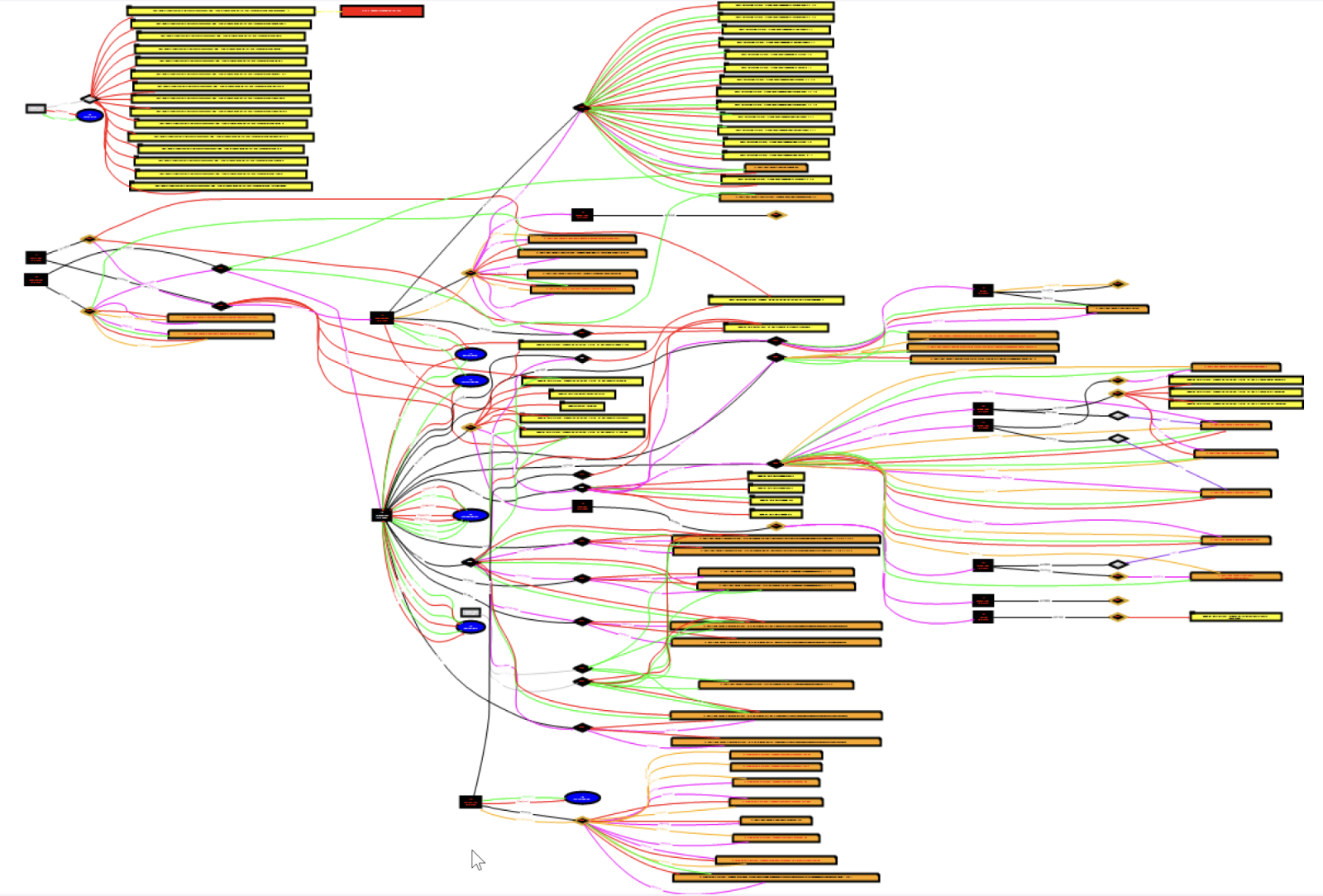
SmartApeSG campaign uses ClickFix page to push NetSupport RAT, (Wed, Nov 12th)
Introduction This diary describes a NetSupport RAT infection I generated in my lab from the SmartApeSG campaign that used a ClickFix-style fake CAPTCHA page. Known as ZPHP or HANEYMANEY, SmartApeSG is a campaign reported as early as June 2024. When it started, this campaign used fake browser update pages. But it currently uses the ClickFix method of fake…
-
ISC Stormcast For Wednesday, November 12th, 2025 https://isc.sans.edu/podcastdetail/9696, (Wed, Nov 12th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Microsoft Patch Tuesday for November 2025, (Tue, Nov 11th)
Today’s Microsoft Patch Tuesday offers fixes for 80 different vulnerabilities. One of the vulnerabilities is already being exploited, and five are rated as critical. Notable Vulnerabilities: %%cve:2025-62215%%: This vulnerability is already being exploited. It is a privilege escalation vulnerability in the Windows Kernel. These types of vulnerabilities are often exploited as part of a more…
-
ISC Stormcast For Tuesday, November 11th, 2025 https://isc.sans.edu/podcastdetail/9694, (Tue, Nov 11th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
It isn’t always defaults: Scans for 3CX usernames, (Mon, Nov 10th)
Today, I noticed scans using the username “FTP_3cx” showing up in our logs. 3CX is a well-known maker of business phone system software [1]. My first guess was that this was a default user for one of their systems. But Google came up empty for this particular string. The 3CX software does not appear to…
-
ISC Stormcast For Monday, November 10th, 2025 https://isc.sans.edu/podcastdetail/9692, (Mon, Nov 10th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Honeypot: Requests for (Code) Repositories, (Sat, Nov 8th)
This is just a quick diary entry to report that I saw requests on my honeypot for (code) repositories: /.git/logs/refs/remotes/origin/main /.git/objects/info /.github /.github/dependabot.yml /.github/funding.yml /.github/ISSUE_TEMPLATE /.gitlab/issue_templates /.gitlab-ci /.git-secret /.svnignore /aws/bucket /s3/backup /s3/bucket /s3/credentials So watch out what you publish online when you deploy a repository to your web site. Didier Stevens Senior handler blog.DidierStevens.com…
-
ISC Stormcast For Friday, November 7th, 2025 https://isc.sans.edu/podcastdetail/9690, (Fri, Nov 7th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.

