-
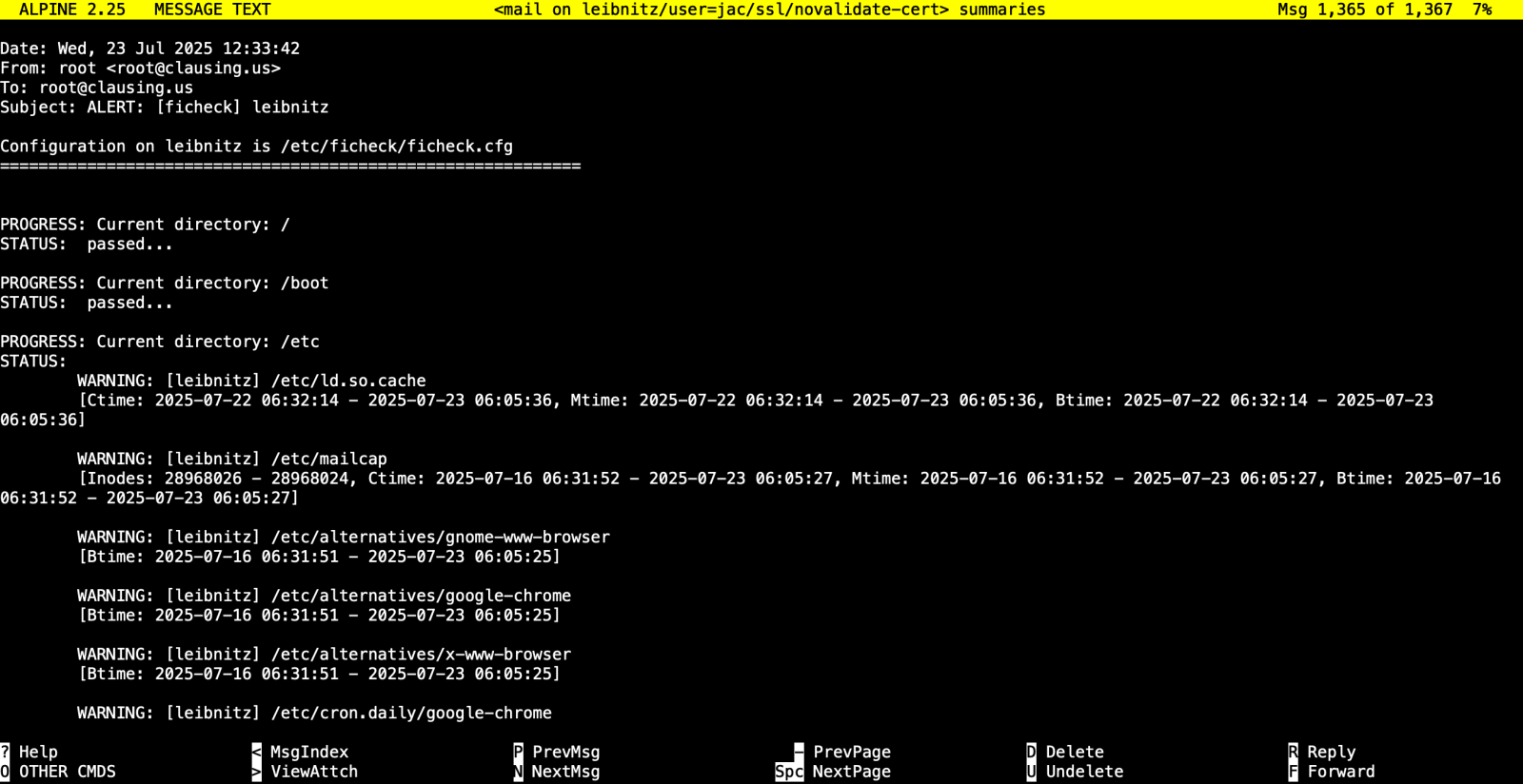
New Tool: ficheck.py, (Thu, Jul 24th)
As I mention every time I teach FOR577, I have been a big fan of file integrity monitoring tools (FIM) since Gene Kim first released Tripwire well over 30 years ago. I’ve used quite a few of them over the years including tripwire, OSSEC, samhain, and aide, just to name a few. For many years,…
-
ISC Stormcast For Thursday, July 24th, 2025 https://isc.sans.edu/podcastdetail/9540, (Thu, Jul 24th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Analyzing Sharepoint Exploits (CVE-2025-53770, CVE-2025-53771), (Wed, Jul 23rd)
A few days after the exploit originally became widely known, there are now many different SharePoint exploit attempts in circulation. We do see some scans by researchers to identify vulnerable systems (or to scan for common artifacts of compromise), and a few variations of the “ToolPane.aspx” URL being hit. Even for our “random” honeypots, the…
-
ISC Stormcast For Wednesday, July 23rd, 2025 https://isc.sans.edu/podcastdetail/9538, (Wed, Jul 23rd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
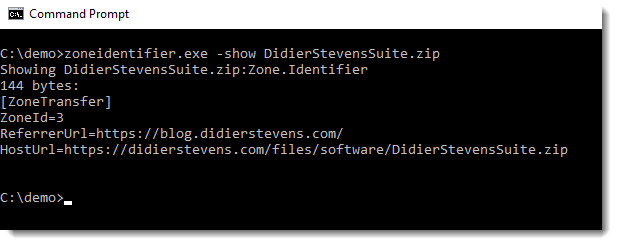
WinRAR MoTW Propagation Privacy, (Tue, Jul 22nd)
Since WinRAR 7.10, not all Mark-of-The-Web data (stored in the Zone.Identifier Alternate Data Stream) is propagated when you extract a file from an archive. Take my DidierStevensSuite.zip file that I downloaded with a browser in normal mode. It has the following Zone.Identifier ADS: Not only does it have a ZoneId field that indicates the origin…
-
Wireshark 4.4.8 Released, (Tue, Jul 22nd)
Wireshark release 4.4.8 fixes 9 bugs. Didier Stevens Senior handler blog.DidierStevens.com (c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Tuesday, July 22nd, 2025 https://isc.sans.edu/podcastdetail/9536, (Tue, Jul 22nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
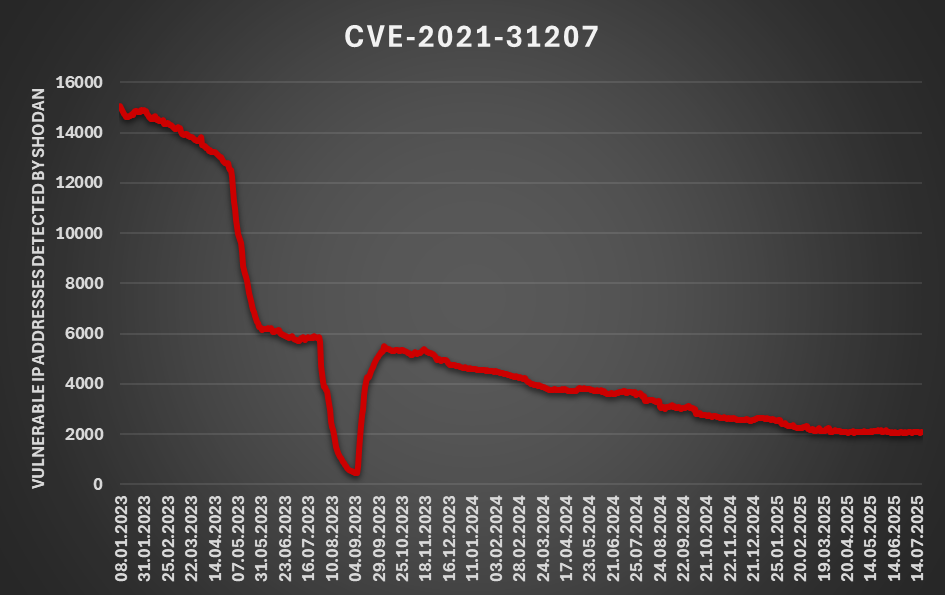
How quickly do we patch? A quick look from the global viewpoint, (Mon, Jul 21st)
Since the ongoing “ToolShell” exploitation campaign, in which threat actors attack on-premise Sharpoint servers using a chain of two recently published vulnerabilities[1,2,3], is still on top of the cyber security news[4,5,6,7], I thought it might be a good time to look at the question of how quickly do we – as a global society –…
-
ISC Stormcast For Monday, July 21st, 2025 https://isc.sans.edu/podcastdetail/9534, (Mon, Jul 21st)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Critical Sharepoint 0-Day Vulnerablity Exploited CVE-2025-53770 (ToolShell), (Sun, Jul 20th)
Microsoft announced yesterday that a newly discovered critical remote code execution vulnerability in SharePoint is being exploited. There is no patch available. As a workaround, Microsoft suggests using Microsoft Defender to detect any attacks. To use Defender, you must first configure the AMSI integration to give Defender visibility into SharePoint. Recent versions of SharePoint have…

