-
ISC Stormcast For Friday, June 6th, 2025 https://isc.sans.edu/podcastdetail/9482, (Fri, Jun 6th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Upcoming DShield Honeypot Changes and Customizations, (Fri, Jun 6th)
There are some upcoming DShield honeypot [1] changes that introduce some opportunities for additional customization and data analysis. For most users, no additional actions are needed. A couple of those changes: dshield.ini file move from /etc/ to /srv/dshield/etc/ – A symbolic link will exist for the previous file location for backward compatibility. If you have…
-
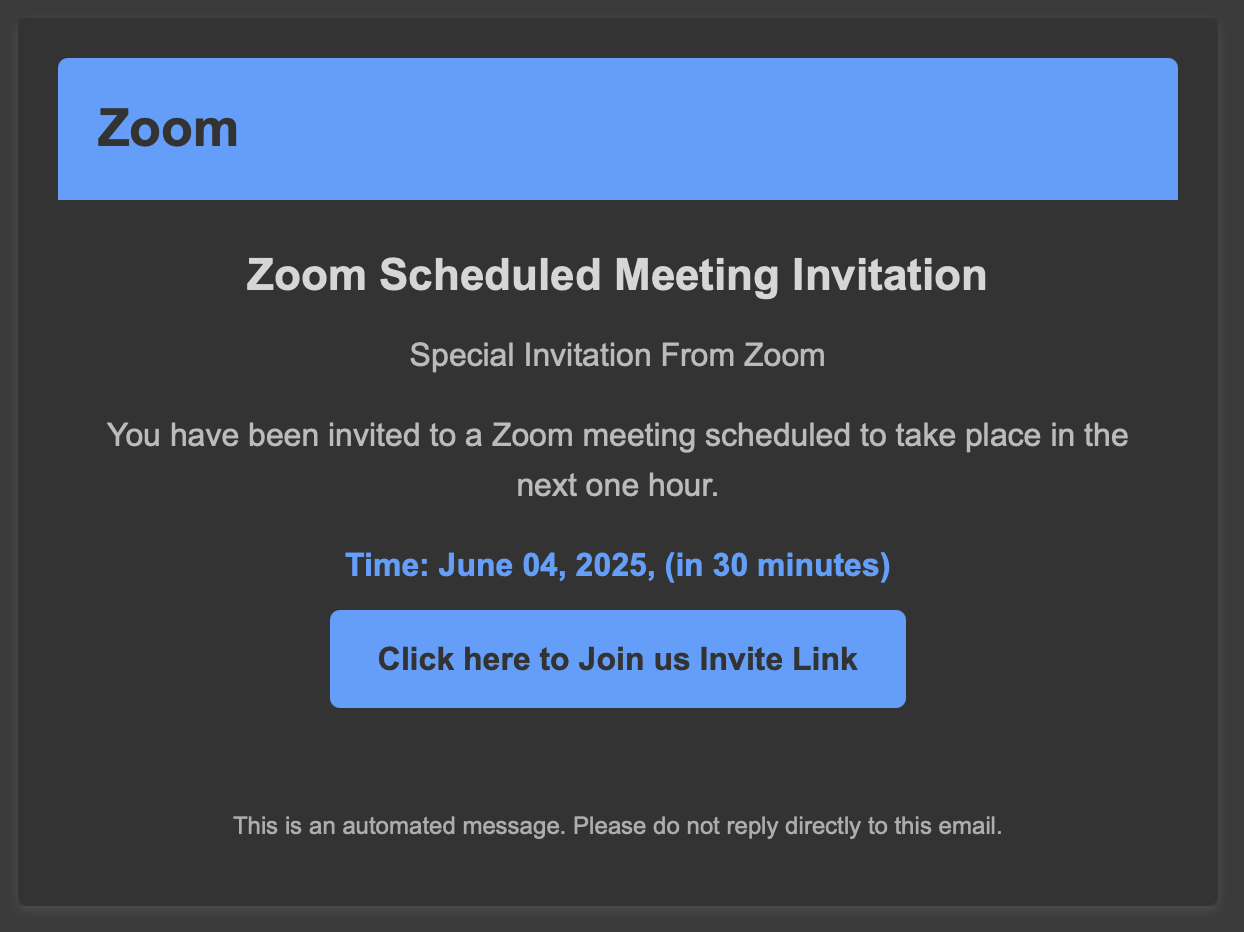
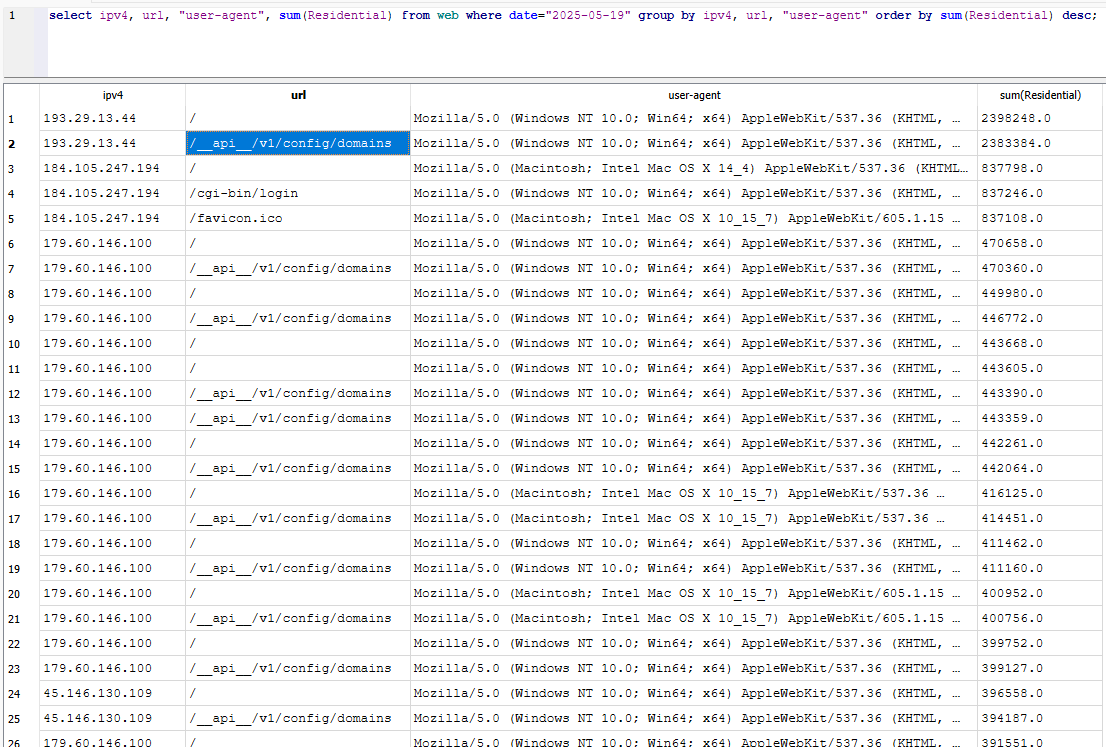
Be Careful With Fake Zoom Client Downloads, (Thu, Jun 5th)
Collaborative tools are really popular these days. Since the COVID-19 pandemic, many people switched to remote work positions and we need to collaborate with our colleagues or customers every day. Tools like Microsoft Teams, Zoom, WebEx, (name your best solution), … became popular and must be regularly updated.Yesterday, I received an interesting email with a fake…
-
ISC Stormcast For Thursday, June 5th, 2025 https://isc.sans.edu/podcastdetail/9480, (Thu, Jun 5th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
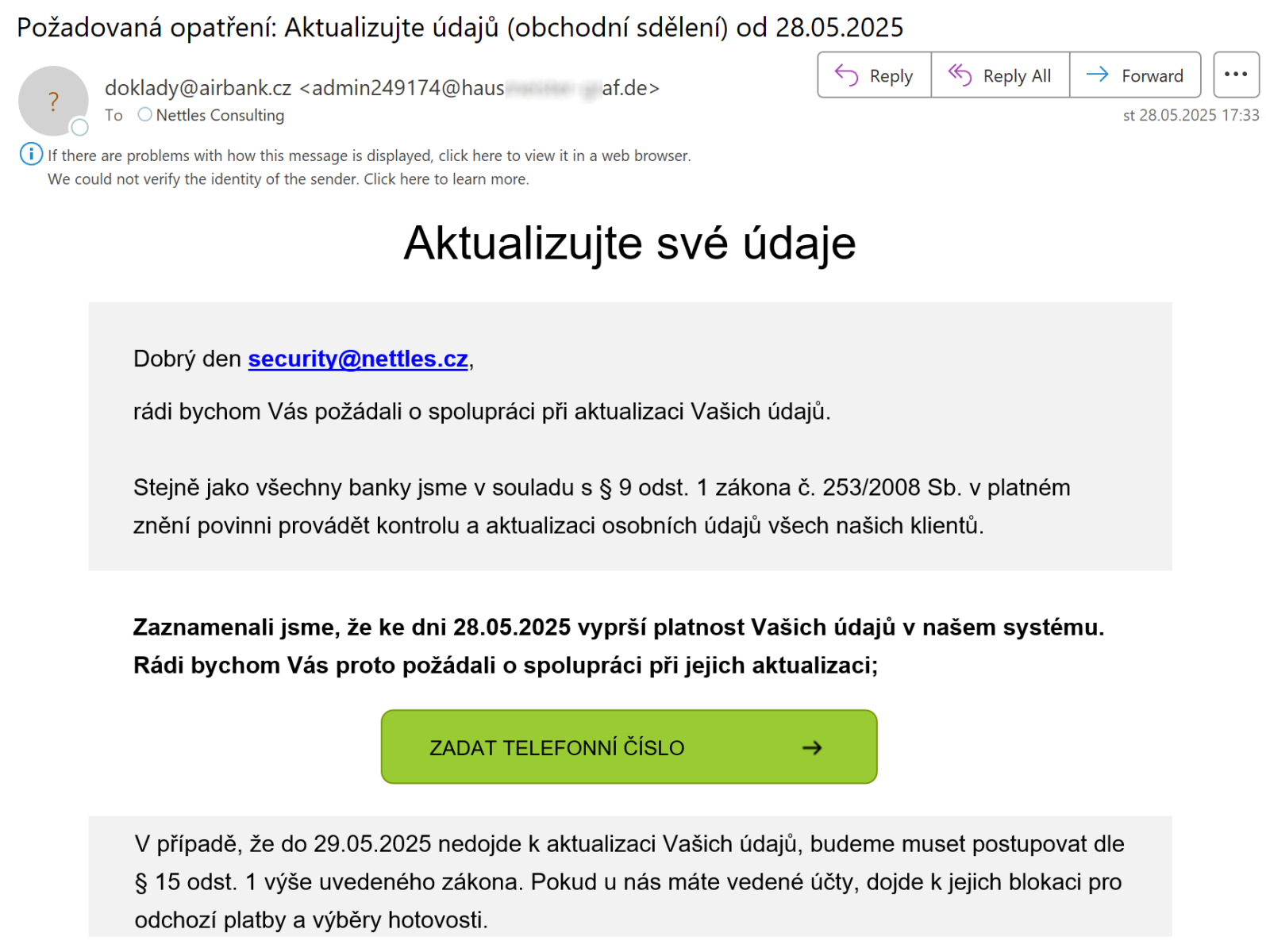
Phishing e-mail that hides malicious link from Outlook users, (Wed, Jun 4th)
I recently came across an interesting phishing e-mail. At first glance, it looked like a “normal” phishing that tried to pass itself off as a message from one of the Czech banks asking account holders to update their information… Nevertheless, when I hovered above the rectangle that a recipient was expected to click on, I…
-
ISC Stormcast For Wednesday, June 4th, 2025 https://isc.sans.edu/podcastdetail/9478, (Wed, Jun 4th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-

vBulletin Exploits (CVE-2025-48827, CVE-2025-48828), (Tue, Jun 3rd)
Last week, Ryan Dewhurst disclosed an interesting and easily exploitable vulnerability in vBulltin. These days, bulletin boards are not quite as popular as they used to be, but they are still being used, and vBulletin is one of the most common commercially supported platforms to create a bulletin board. The vulnerability is remarkable as it exemplifies…
-
ISC Stormcast For Tuesday, June 3rd, 2025 https://isc.sans.edu/podcastdetail/9476, (Tue, Jun 3rd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Monday, June 2nd, 2025 https://isc.sans.edu/podcastdetail/9474, (Mon, Jun 2nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
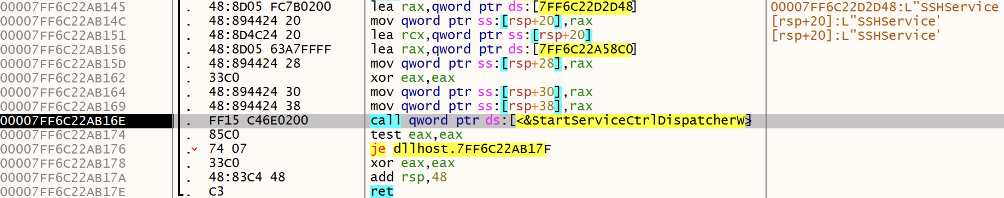
Simple SSH Backdoor, (Mon, Jun 2nd)
For most system and network administrators, the free SSH client Putty has been their best friend for years! This tool was also (ab)used by attackers that deployed a trojanized version[1]. Microsoft had the good idea to include OpenSSH (beta version) in Windows 10 Fall Creators Update. One year later, it became a default component with Windows…

