-

XORsearch: Searching With Regexes, (Mon, Apr 7th)
Xavier asked me a question from one of his FOR610 students: “how can you perform a regex search with XORsearch”? XORsearch is a tool like grep but it performs a brute-force attack on the input file, trying out different encodings like XOR. You can give it a string to search for, but not a regular…
-
ISC Stormcast For Monday, April 7th, 2025 https://isc.sans.edu/podcastdetail/9396, (Mon, Apr 7th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
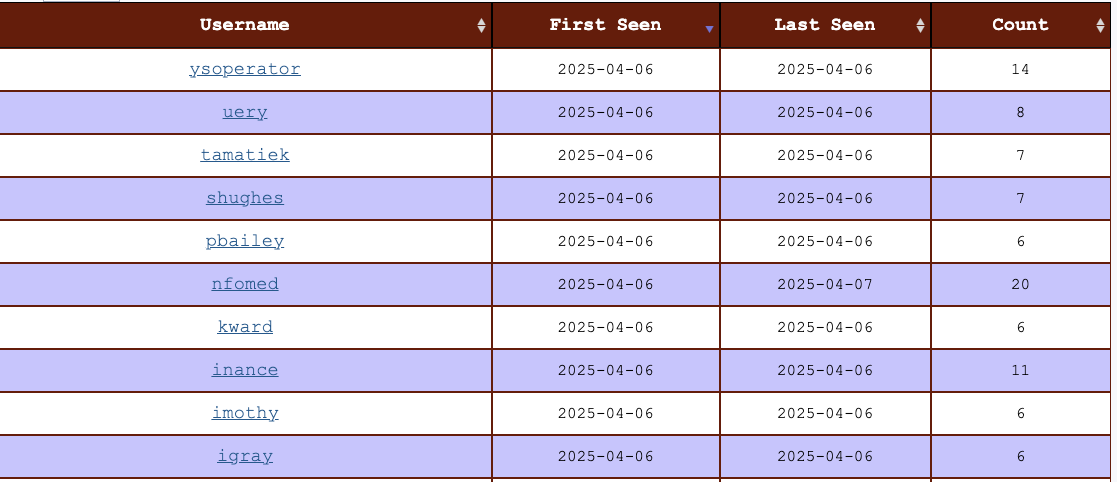
New SSH Username Report, (Sun, Apr 6th)
As you may have noticed by some of my recent diaries, I have spent a bit more time on ssh and telnet credentials. These credentials are collected by Cowrie, the amazing full features SSH and Telnet honeypot maintained by Michel Oosterhof. Cowrie is installed as a component if you install our DShield honeypot. One very simple…
-
ISC Stormcast For Friday, April 4th, 2025 https://isc.sans.edu/podcastdetail/9394, (Fri, Apr 4th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Thursday, April 3rd, 2025 https://isc.sans.edu/podcastdetail/9392, (Thu, Apr 3rd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Exploring Statistical Measures to Predict URLs as Legitimate or Intrusive [Guest Diary], (Wed, Apr 2nd)
[This is a Guest Diary by Gregory Weber, an ISC intern as part of the SANS.edu BACS program] For the last 5 months, as part of my BACS internship with SANS, I have monitored two deployments of a DShield Sensor, sometimes referred to as a honeypot. The DShield sensor offers multiple attack surfaces including Telnet…
-
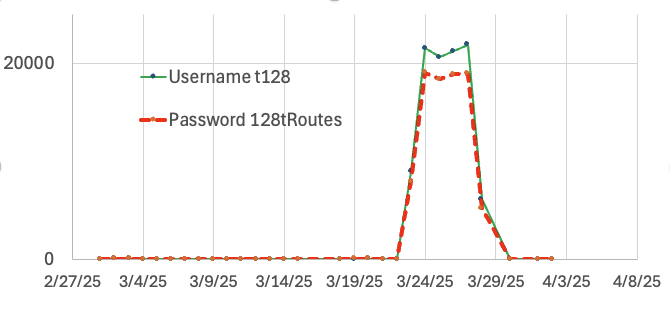
Surge in Scans for Juniper “t128” Default User, (Wed, Apr 2nd)
Last week, I noticed a surge in scans for the username “t128”. This username, accompanied by the password “128tRoutes,” is a well-known default account for Juniper’s Session Smart Networking Platform (or “SSR” for “Session Smart Routing”). The username and password are a bit “odd”. Juniper acquired a company called “128 Technologies” a few years ago,…
-
ISC Stormcast For Wednesday, April 2nd, 2025 https://isc.sans.edu/podcastdetail/9390, (Wed, Apr 2nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Tuesday, April 1st, 2025 https://isc.sans.edu/podcastdetail/9388, (Tue, Apr 1st)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Apple Patches Everything: March 31st 2025 Edition, (Mon, Mar 31st)
Today, Apple released updates across all its products: iOS, iPadOS, macOS, tvOS, visionOS, Safari, and XCode. WatchOS was interestingly missing from the patch lineup. This is a feature update for the operating systems, but we get patches for 145 different vulnerabilities in addition to new features. This update includes a patch for CVE-2025-24200 and CVE-2025-24201, two already…

