-
ISC Stormcast For Wednesday, April 29th, 2026 https://isc.sans.edu/podcastdetail/9910, (Wed, Apr 29th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
HTTP Requests with X-Vercel-Set-Bypass-Cookie Header, (Tue, Apr 28th)
This weekend, we saw a few requests to our honeypot that included an “X-Vercel-Set-Bypass-Cookie” header. A sample request: GET / HTTP/1.1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.0.0 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/ *;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate, br Cache-Control: no-cache Pragma: no-cache Connection: keep-alive X-Vercel-Set-Bypass-Cookie: samesite-none-secure Upgrade-Insecure-Requests: 1 X-Forwarded-From: 21.235.92.139 X-Real-Iphone: 21.235.92.139 Referer: [redacted, same…
-
ISC Stormcast For Tuesday, April 28th, 2026 https://isc.sans.edu/podcastdetail/9908, (Tue, Apr 28th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
TeamPCP Supply Chain Campaign: Update 008 – 26-Day Pause Ends with Three Concurrent Compromises (Checkmarx KICS, Bitwarden CLI Cascade, xinference PyPI), CanisterSprawl npm Worm Identified, and Tier 1 Coverage Returns, (Mon, Apr 27th)
This update succeeds TeamPCP Supply Chain Campaign Update 007, published April 8, 2026, which left the campaign in credential-monetization mode following the Cisco source code theft via Trivy-linked credentials, Google GTIG’s formal designation of the operators as UNC6780 (with their credential stealer named SANDCLOCK), and the lapsed CISA KEV remediation deadline for CVE-2026-33634 with no standalone…
-
ISC Stormcast For Friday, April 24th, 2026 https://isc.sans.edu/podcastdetail/9906, (Fri, Apr 24th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Apple Patches Exploited Notification Flaw, (Thu, Apr 23rd)
Apple yesterday released iOS/iPadOS 26.4.2 and iOS/iPadOS 18.7.8. This update fixes a single Notification Services vulnerability, CVE-2026-28950: Impact: Notifications marked for deletion could be unexpectedly retained on the device Description: A logging issue was addressed with improved data redaction. Apple did not mark the vulnerability as exploited. However, recent news articles reported that the FBI…
-
ISC Stormcast For Thursday, April 23rd, 2026 https://isc.sans.edu/podcastdetail/9904, (Thu, Apr 23rd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Wednesday, April 22nd, 2026 https://isc.sans.edu/podcastdetail/9902, (Wed, Apr 22nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
[Guest Diary] Beyond Cryptojacking: Telegram tdata as a Credential Harvesting Vector, Lessons from a Honeypot Incident, (Wed, Apr 22nd)
[This is a Guest Diary by L. Carty, an ISC intern as part of the SANS.edu Bachelor’s Degree in Applied Cybersecurity (BACS) program [1].] Introduction A few weeks ago, my honeypot logged an incident that changed how I think about modern attacks. A threat actor broke into my system using weak SSH credentials and immediately…
-
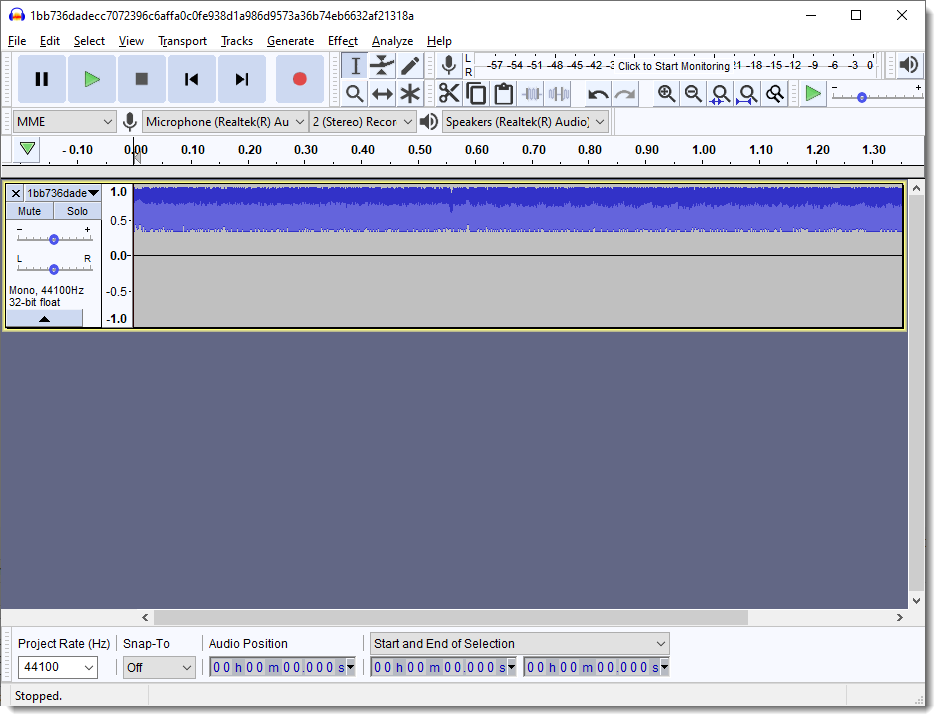
A .WAV With A Payload, (Tue, Apr 21st)
There have been reports of threat actors using a .wav file as a vector for malware. It’s a proper .wav file, but they didn’t use staganography. The .wav file will play, but you’ll just hear noise: That’s because the TAs have just replaced the bytes that encode the sound with the BASE64 representation of their…

