Introduction
This diary provides indicators from a Lumma Stealer infection that was followed by Sectop RAT (ArechClient2). I searched for cracked versions of popular copyright-protected software, and I downloaded the initial malware after following the results of one such search. This is a common distribution technique for various families of malware, and I often find Lumma Stealer this way.
In this case, the initial malware for Lumma Stealer was delivered as a password-protected 7-zip archive. The extracted malware is an inflated Windows executable (EXE) file at 806 MB. The EXE is padded with null-bytes (0x00), a technical which increases the EXE size while allowing the compressed archive file to be much smaller. The password-protected archive and inflated EXE file are designed to avoid detection.
Images from the infection
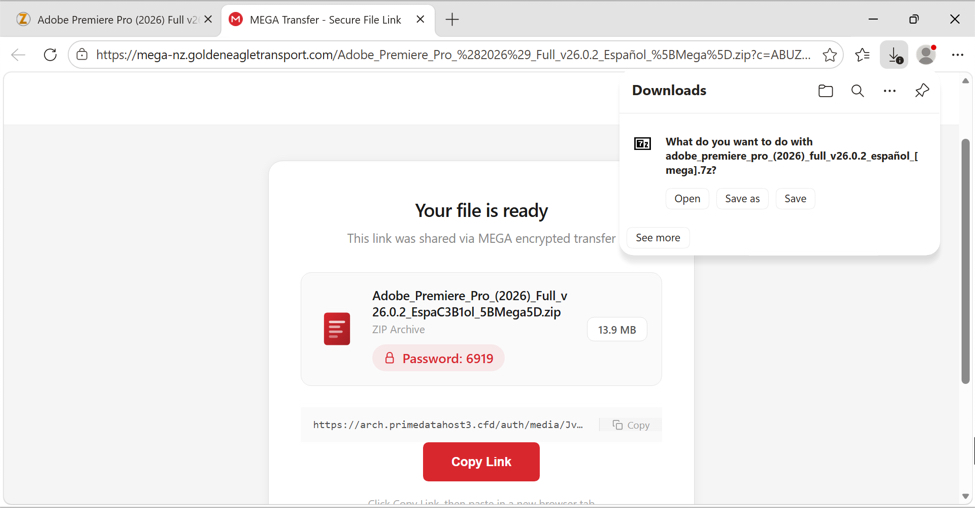
Shown above: Example of a page with instructions to download the initial malware file.
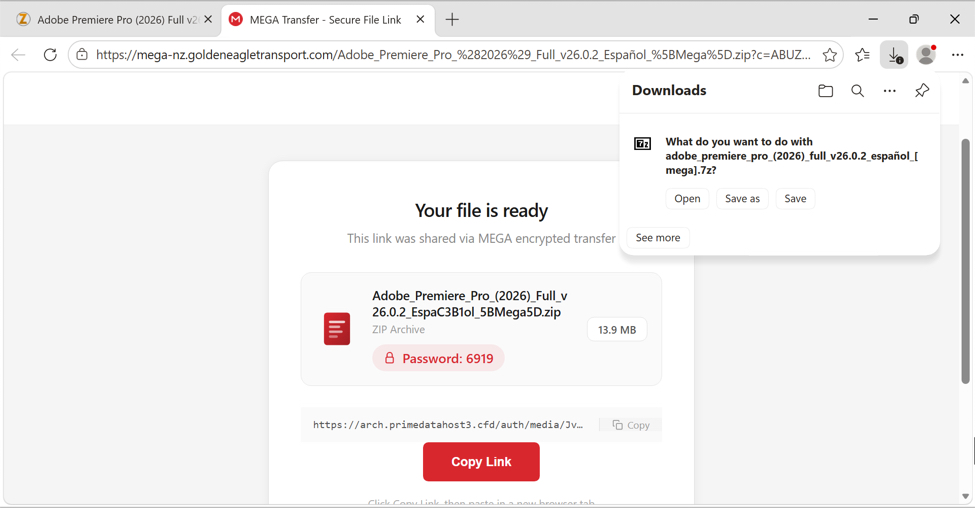
Shown above: Traffic from the infection filtered in Wireshark.
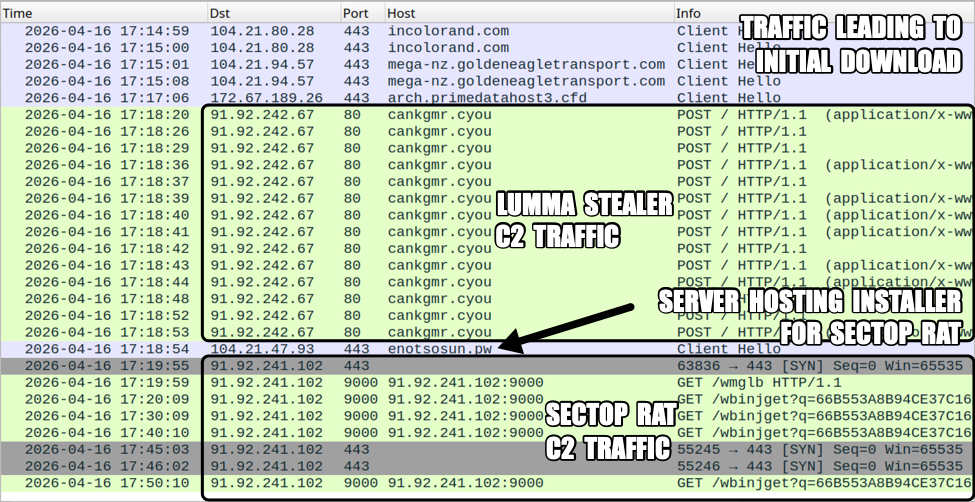
Shown above: Sectop RAT persistent on an infected Windows host.
Indicators of Compromise
Example of download link from the site advertising cracked versions of copyright-protected software:
hxxps[:]//incolorand[.]com/how-visual-patch-enhances-ui-consistency-across-releases/?utm_source={CID}&utm_term=Adobe%20Premiere%20Pro%20(2026)%20Full%20v26.0.2%20Espa%C3%B1ol%20[Mega]&utm_content={SUBID1}&utm_medium={SUBID2}
Example of URL for page with the file download instructions:
hxxps[:]//mega-nz.goldeneagletransport[.]com/Adobe_Premiere_Pro_%282026%29_Full_v26.0.2_Espa%C3%B1ol_%5BMega%5D.zip?c=ABUZ4WkRgQUA_YUCAFVTFwASAAAAAACh&s=360721
Example of URL for file download from site above site impersonating MEGA:
hxxps[:]//arch.primedatahost3[.]cfd/auth/media/JvWcFd5vUoYTrImvtWQAASTh/Adobe_Premiere_Pro_(2026)_Full_v26.0.2_Espa%C3%B1ol_%5BMega%5D.zip
Downloaded file:
- SHA256 hash: c7489e3bf546c5f2d958ac833cc7dbca4368dfba03a792849bc99c48a6b2a14f
- File size: 3,888,051 bytes
- File name: adobe_premiere_pro_(2026)_full_v26.0.2_espan?ol_[mega].7z
- File type: 7-zip archive data, version 0.4
- File description: Password-protected 7-zip archive
- Password: 6919
Extracted malware:
- SHA256 hash: 4849f76dafbef516df91fecfc23a72afffaf77ade51f805eae5ad552bed88923
- File size: 806,127,604 bytes
- File name: appFile.exe
- File type: PE32 executable (GUI) Intel 80386, for MS Windows
- File description: Inflated Windows EXE file for Lumma Stealer, padded with null-bytes
Deflated malware:
- SHA256 hash: 353ddce78d58aef2083ca0ac271af93659cf0039b0b29d0d169fc015bd3610bc
- File size: 7,114,156 bytes
- File type: PE32 executable (GUI) Intel 80386, for MS Windows
- File description: Above appFile.exe with most of null-byte padding removed
- Any.Run sandbox analysis
- Triage sandbox analysis
Lumma Stealer command and control (C2) domains from Triage sandbox analysis:
- cankgmr[.]cyou
- carytui[.]vu
- decrnoj[.]club
- genugsq[.]best
- longmbx[.]click
- mushxhb[.]best
- pomflgf[.]vu
- strikql[.]shop
- ulmudhw[.]shop
Follow-up malware:
- SHA256 hash: d9b576eb6827f38e33eda037d2cda4261307511303254a8509eeb28048433b2f
- File size: 16,450,560 bytes
- File type: PE32+ executable (DLL) (GUI) x86-64, for MS Windows
- Retrieved from: hxxps[:]//enotsosun[.]pw/NetGui.dll
- Saved to: C:Users[username]AppDataLocalTemp16XBPQ29ZBG94TYNOA.dll
- File description: 64-bit DLL to install and run Sectop RAT (ArechClient2)
- Run method: rundll32 [file path],LoadForm
- Any.Run sandbox analysis
- Triage sandbox analysis
Example of Sectop RAT C2 traffic from an infected Windows host:
- hxxp[:]//91.92.241[.]102:9000/wmglb
- hxxp[:]//91.92.241[.]102:9000/wbinjget?q=66B553A8B94CE37C16F4EBC863D51FCC
- tcp[:]//91.92.241[.]102:443/ – encoded or otherwise encrypted traffic (not HTTPS/TLS)
—
Bradley Duncan
brad [at] malware-traffic-analysis.net
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.