-
TeamPCP Supply Chain Campaign: Activity Through 2026-05-24, (Mon, May 25th)
TeamPCP now operates across three package ecosystems in parallel, it reached GitHub’s own internal codebase, it trojanized an officially Microsoft-published Python SDK, and it appears to have open-sourced its own framework on GitHub. Bottom line up front Three escalations stacked inside a single week. First, GitHub’s CISO Alexis Wales publicly named a malicious Nx Console…
-
Wireshark 4.6.6 Released, (Sun, May 24th)
Wireshark release 4.6.6 fixes 1 vulnerability and 11 bugs. For WIndows, Npcap is updated to version 1.88. Didier Stevens Senior handler blog.DidierStevens.com (c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
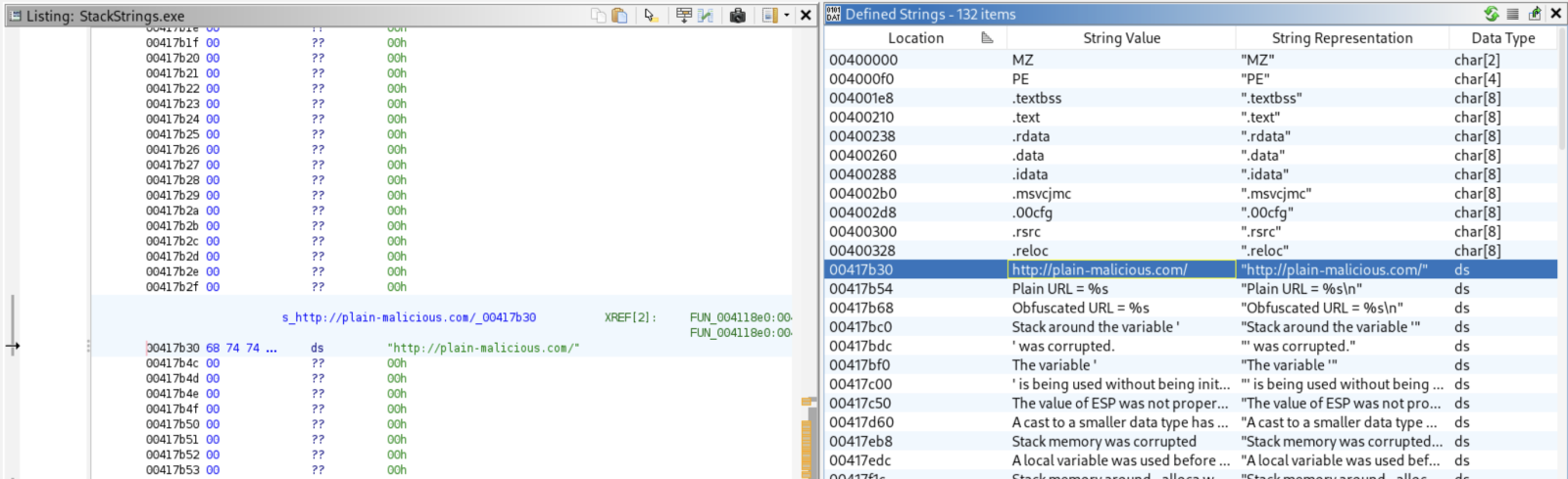
An Example of Stack String in High Level Language, (Sat, May 23rd)
This week, I’m attending the SEC670[1] training (“Red Teaming Tools – Developing Windows Implants, Shellcode, Command and Control”). From my point of view, this training fits perfectly with FOR610 or FOR710 (malware analysis) because it addresses malware from the opposite: Instead of performing reverse engineering, you write malicious code! Always interesting to have another point…
-
Cross-Platform NPM Stealer, (Fri, May 22nd)
I found a Node.js stealer that looked pretty well obfuscated. The file was not running out-of-the-box because it was uploaded on VT as “extracted-decoded.js” (and reformated). The SHA256 is 049300aa5dd774d6c984779a0570f59610399c71864b5d5c2605906db46ddeb9[1]. It did not run properly in a sandbox so only a static analysis was performed. The key point is that it is a cross-platform stealer…
-
ISC Stormcast For Friday, May 22nd, 2026 https://isc.sans.edu/podcastdetail/9942, (Fri, May 22nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Selective HTTP Proxying in Linux, (Thu, May 21st)
Recently, Rob wrote about a tool, Proxifier, that can intercept requests from specific processes. Proxifier is available for Windows, macOS, and Android. But I have not seen a generic Linux option yet. The advantage of a tool like Proxifier is the ability to target specific software. For debugging, reverse engineering, and similar tasks, selecting a…
-
ISC Stormcast For Thursday, May 21st, 2026 https://isc.sans.edu/podcastdetail/9940, (Thu, May 21st)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Wednesday, May 20th, 2026 https://isc.sans.edu/podcastdetail/9938, (Wed, May 20th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Tuesday, May 19th, 2026 https://isc.sans.edu/podcastdetail/9936, (Tue, May 19th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
TeamPCP Supply Chain Campaign: Activity Through 2026-05-17, (Mon, May 18th)
Since the last update, the TeamPCP supply chain campaign produced its loudest stretch since the March Trivy disclosure: an officially confirmed Checkmarx Jenkins plugin compromise and a new self-spreading Mini Shai-Hulud worm across npm and PyPI. Bottom line up front Two TeamPCP events broke within 48 hours of each other and doubled attention on the campaign.…

