-
![[Guest Diary] New Malware Libraries means New Signatures, (Fri, May 15th)](/wp-content/uploads/2026/05/figure1_cowrie_session-VB4Myn.png)
[Guest Diary] New Malware Libraries means New Signatures, (Fri, May 15th)
This is a Guest Diary by Gokul Prema Thangavel, an ISC intern as part of the SANS.edu Bachelor Degree Program. Introduction The SHA-256 a8460f446be540410004b1a8db4083773fa46f7fe76fa84219c93daa1669f8f2 is one of the most-observed Outlaw / Shellbot artifacts on the public internet. VirusTotal first ingested it on 5 July 2018 [2]. It is the SHA-256 of the authorized_keys file written…
-
ISC Stormcast For Friday, May 15th, 2026 https://isc.sans.edu/podcastdetail/9934, (Fri, May 15th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
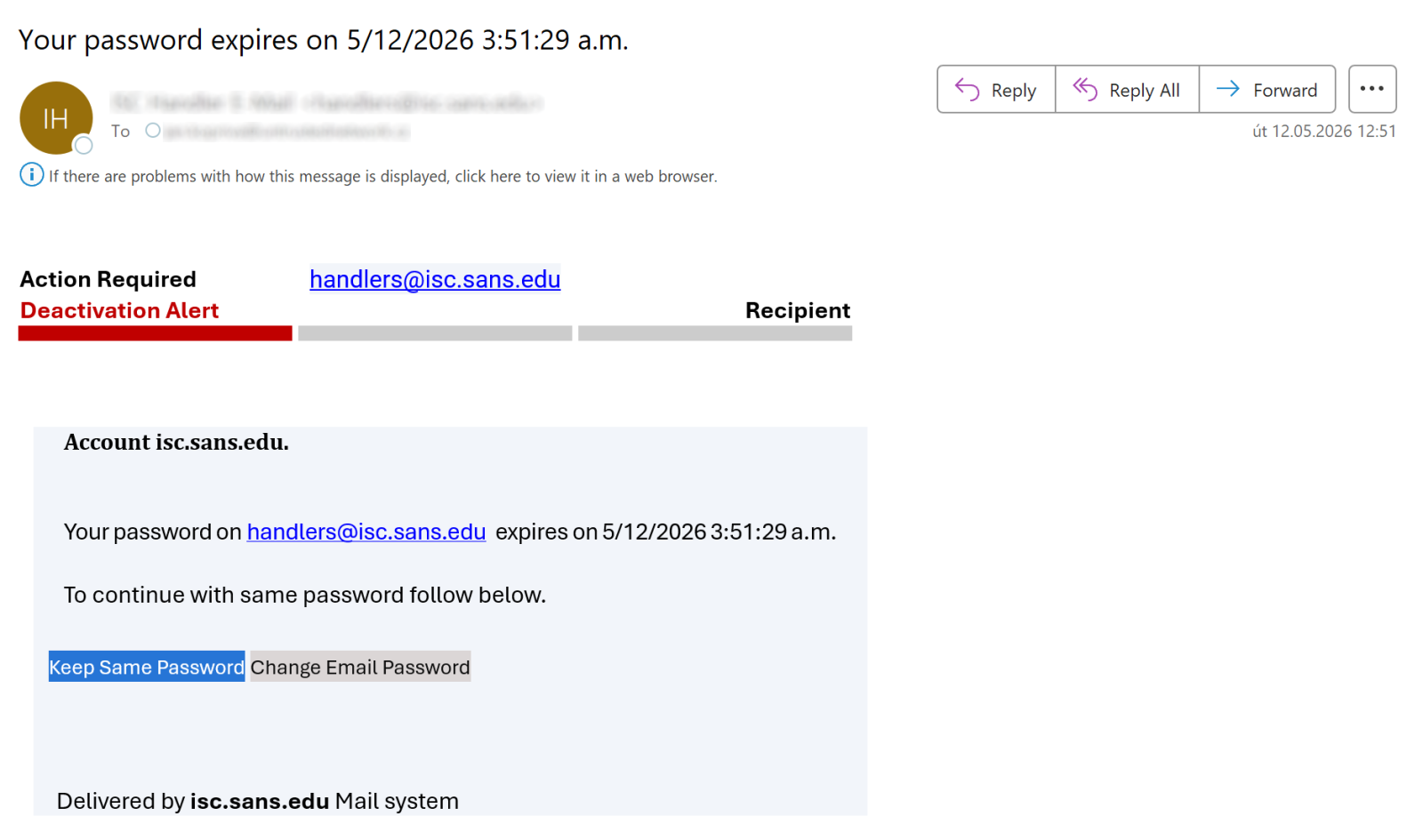
Simple bypass of the link preview function in Outlook Junk folder, (Thu, May 14th)
Besides serving as a place where Microsoft Outlook places suspected spam, the Outlook Junk folder has one additional function that can be quite helpful when it comes to identifying malicious messages. Any e-mail placed in this folder is stripped of all formatting, and destinations of all links included in the message become visible to the…
-
ISC Stormcast For Thursday, May 14th, 2026 https://isc.sans.edu/podcastdetail/9932, (Thu, May 14th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
![[GUEST DIARY] Tearing apart website fraud to see how it works., (Wed, May 13th)](/wp-content/uploads/2026/05/1-VTresults-d7xogZ.png)
[GUEST DIARY] Tearing apart website fraud to see how it works., (Wed, May 13th)
[This is a Guest Diary by Joshua Nikolson, an ISC Intern and part of the SANS.edu Bachelor’s degree in Applied Cybersecurity (BACS) program.] Introduction One day at work, a friend messaged me, “How do you check a website to see if it’s legit?” This friend recently received a phishing text message from a “bank”,…
-
ISC Stormcast For Wednesday, May 13th, 2026 https://isc.sans.edu/podcastdetail/9930, (Wed, May 13th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
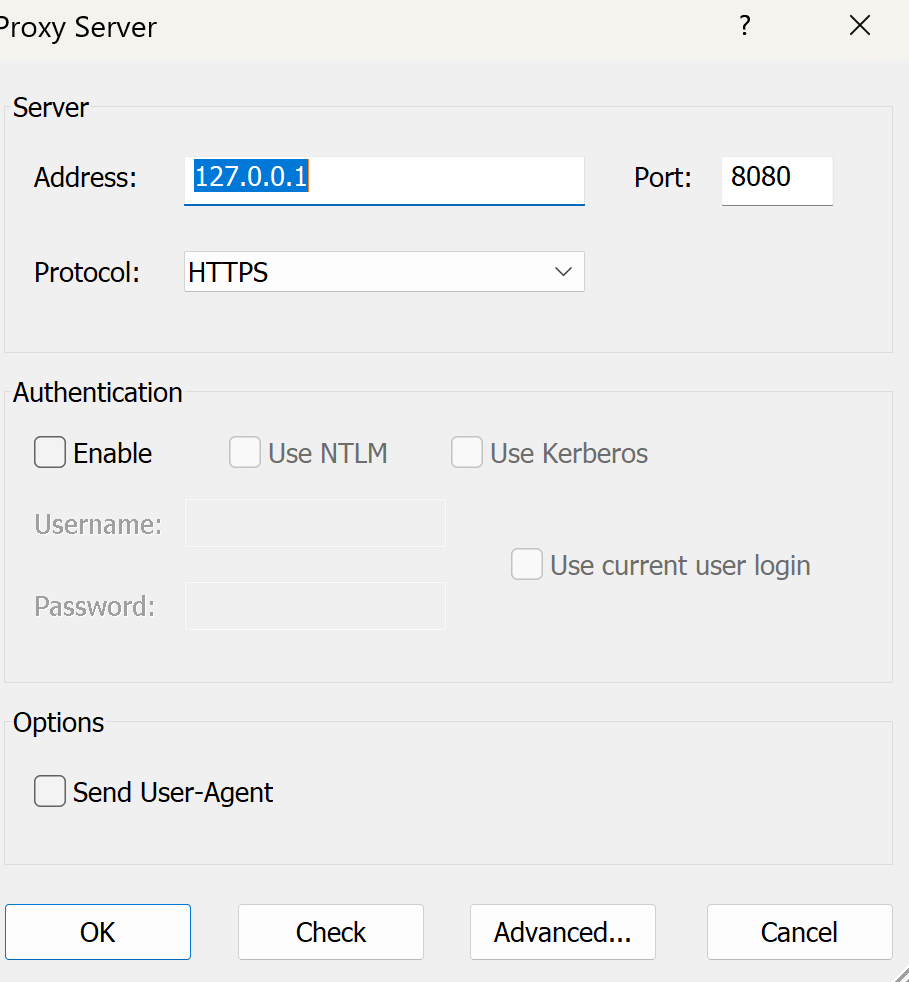
Proxying the Unproxyable? Sending EXE traffic to a Proxy, (Wed, May 13th)
.. if “unproxyable” is a word that is .. I had a recent engagement where I had to look at the network traffic generated by a Windows executable. Unfortunately, it was all TLS, and all TLS1.3 to boot. So from a PCAP all I got was a whole lot of “yup, that’s encrypted”, and since…
-
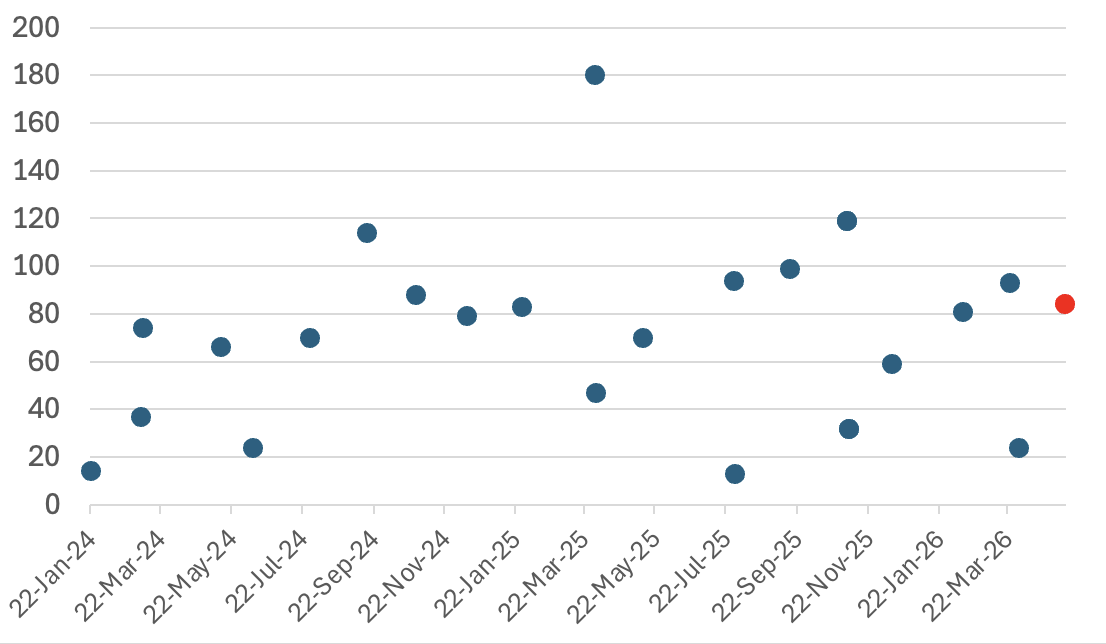
Microsoft May 2026 Patch Tuesday, (Tue, May 12th)
Today’s Microsoft patch Tuesday fixes 137 different vulnerabilities. In addition, the update addresses 137 Chromium-related issues affecting Microsoft Edge. There are no already disclosed or already exploited vulnerabilities included in today’s patches. I removed the Chromium issues from the table below and included only the 137 Microsoft issues to make it more readable. Note that issues…
-
ISC Stormcast For Tuesday, May 12th, 2026 https://isc.sans.edu/podcastdetail/9928, (Tue, May 12th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Apple Patches Everything, (Mon, May 11th)
Apple today released its typical feature update across it’s operating systems (iOS, iPadOS, macOS, tvOS, watchOS, vision OS). With this update, Apple patched 84 different vulnerabilities. Updates are available for the “26” series of operating systems, as well as for the previous “18” version of iOS/iPadOS, and two versions back for macOS (version 14 and…

