-
ISC Stormcast For Monday, December 2nd, 2024 https://isc.sans.edu/podcastdetail/9236, (Mon, Dec 2nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
From a Regular Infostealer to its Obfuscated Version, (Sat, Nov 30th)
There are many malicious scripts available on the Internet. Github has plenty of info stealers and RATs made available “for testing or research purposes”. Here is one that I found recently: Trap-Stealer[1]. Often those scripts are pretty well obfuscated to pass through security controls and make Security Analysts’ life harder. Let’s review a practical example.…
-
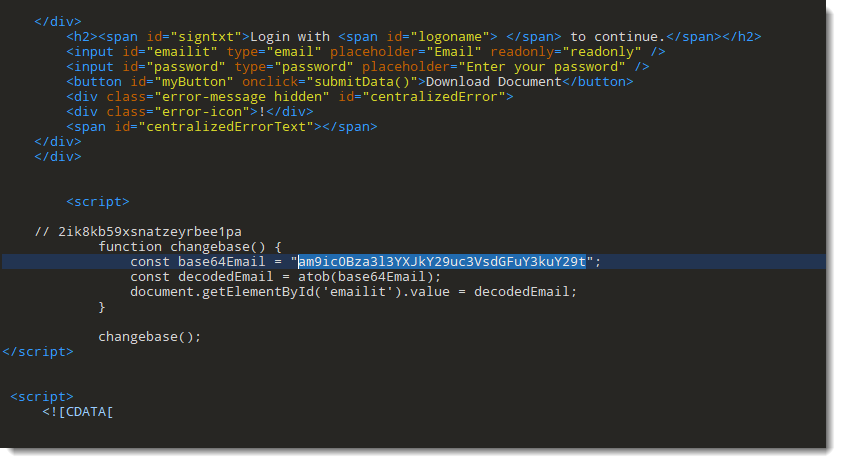
Quickie: Mass BASE64 Decoding, (Fri, Nov 29th)
I was asked how one can decode a bunch of BASE64 encoded IOCs with my tools. I’m going to illustrate my method using the phishing SVG samples I found on VirusTotal (see “Increase In Phishing SVG Attachments“). In these phishing SVG files, the victim’s email address is encoded in BASE64: With grep, I can select…
-
SANS ISC Internship Setup: AWS DShield Sensor + DShield SIEM [Guest Diary], (Tue, Nov 26th)
[This is a Guest Diary by John Paul Zaguirre , an ISC intern as part of the SANS.edu BACS program] Introduction This is a blog post documentation on how to set up the DShield Sensor in AWS, DShield SIEM locally, and connecting them both. I initially setup a Raspberry Pi5 to use as a DShield…
-
ISC Stormcast For Wednesday, November 27th, 2024 https://isc.sans.edu/podcastdetail/9234, (Wed, Nov 27th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
![[Guest Diary] Using Zeek, Snort, and Grafana to Detect Crypto Mining Malware, (Tue, Nov 26th)](/wp-content/uploads/2024/11/2024-11-27_figure1-R9o2ix.png)
[Guest Diary] Using Zeek, Snort, and Grafana to Detect Crypto Mining Malware, (Tue, Nov 26th)
[This is a Guest Diary by David Fitzmaurice, an ISC intern as part of the SANS.edu Bachelor’s Degree in Applied Cybersecurity (BACS) program [1]. Over the last six months there have been frequent SSH connections leaving versions of the RedTail malware on my DShield Honeypot [2]. This variation of the malware is placed on a…
-
ISC Stormcast For Tuesday, November 26th, 2024 https://isc.sans.edu/podcastdetail/9232, (Tue, Nov 26th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
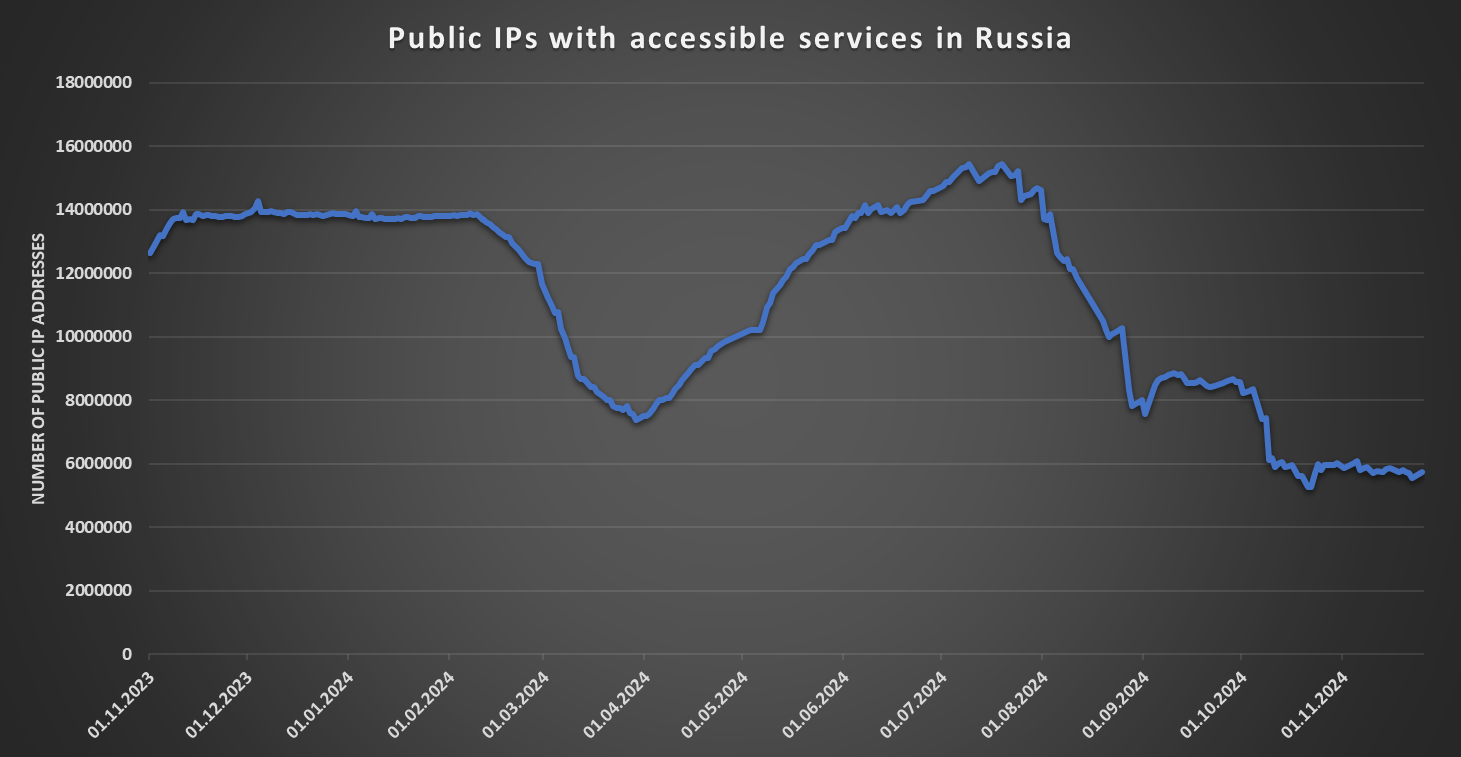
The strange case of disappearing Russian servers, (Mon, Nov 25th)
Few months ago, I noticed that something strange was happening with the number of servers seen by Shodan in Russia… In order to identify any unusual changes on the internet that might be worth a closer look, I have put together a simple script few years ago. It periodically goes over data that was gathered…
-
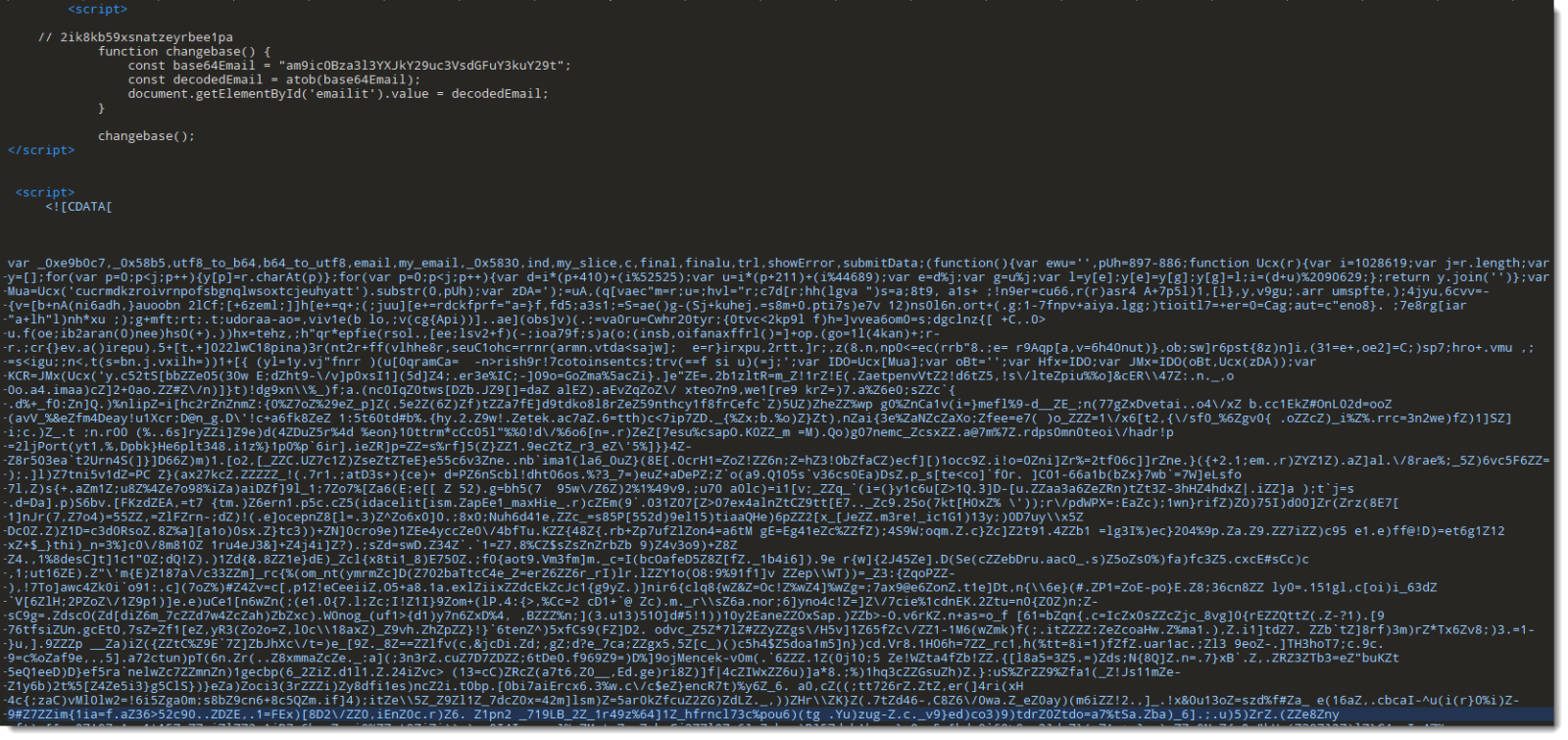
Quick & Dirty Obfuscated JavaScript Analysis, (Sun, Nov 24th)
As mentioned in diary entry “Increase In Phishing SVG Attachments“, I have a phishing SVG sample with heavily obfuscated JavaScript. As I didn’t want to spend time doing static analysis, I did a quick dynamic analysis instead. TL;DR: I open the SVG file in a VM disconnected from the Internet, and use Edge’s developer tools…
-
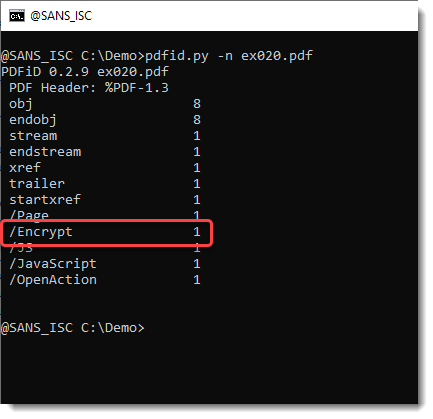
Decrypting a PDF With a User Password, (Sat, Nov 23rd)
In diary entry “Analyzing an Encrypted Phishing PDF“, I decrypted a phishing PDF document. Because the PDF was encrypted for DRM (owner password), I didn’t have to provide a password. What happens if you try this with a PDF encrypted for confidentiality (user password), where a password is needed to open the document? The PDF…

