This is fork from the original work by Scott Jensen [1][2] originally published here as guest diary part of the SANS.edu BACS program. This update has a number of new features now available in Github [4].
The docker compose is custom built to be used with the DShield Honeypot [3][6] to collect, store, parse sensor logs and display the data in a visual and easy way to search and analyze them for research purposes. The assume the DShield sensor is already installed in a Raspberry using PI Raspbian OS or a system running Ubuntu 20.04 LTS either in your network or in the cloud of your choice.
Suggested Setup of ELK Server Based on Ubuntu
Ubuntu 20.04 LTS Live Server 64-Bit
Minimum 8+ GB RAM
If the amount of RAM assigned to each container (see below) is more than 2GB, consider increasing the server RAM capacity.
4-8 Cores
Minimum 40 GB partition assigned to /var/lib/docker
Setting Up Docker
The instructions to setup docker and Elasticsearch are listed here.
The docker package comes setup with the fleet-server and the elastic-agent pre-loaded in docker with 350+ integration for collecting and analyzing data which can be used to add threat intel to ELK, collect netflow data with softflowd or any other logs you want to send to ELK. Docker compose is configured with the following components:
Kibana
Elasticsearch
Logstash
Elastic-Agent
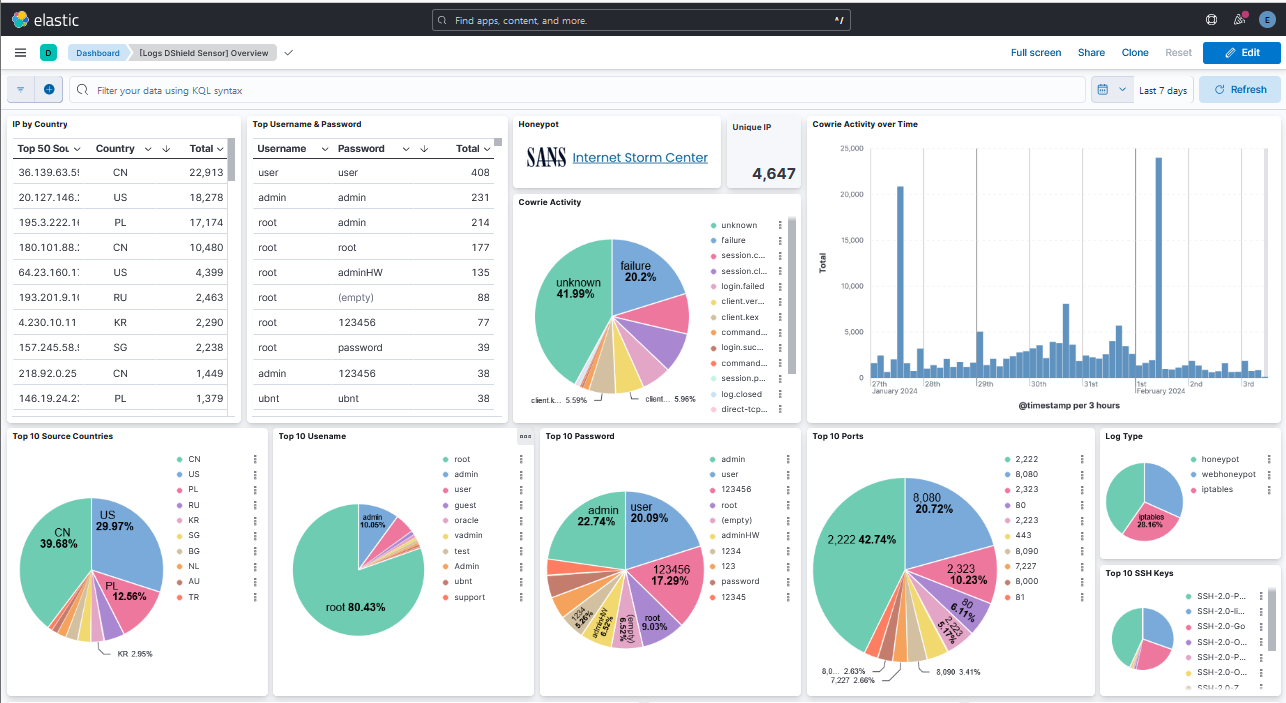
Example of DShield Dashboard
Dashboard [Logs DShield Sensor] Overview
Traffic & Log Analysis
This section contains direct link to CyberGordon which will query multiple sites for the selected hashes. If the ttylogs DShield sensor logs are collected, they can be moved over to the ELK server for review.
Traffic Analysis, Location and Network Owner
This section contains direct link to CyberGordon, Censys & Shodan.
DShield sensor TTYLog Capture Activity
[1] https://isc.sans.edu/diary/DShield+Sensor+Monitoring+with+a+Docker+ELK+Stack+Guest+Diary/30118
[2] https://github.com/fkadriver/Dshield-ELK
[3] https://isc.sans.edu/tools/honeypot/
[4] https://github.com/bruneaug/DShield-SIEM/tree/main
[5] https://github.com/bruneaug/DShield-SIEM/blob/main/README.md#install-docker
[6] https://github.com/DShield-ISC/dshield
[7] https://www.sans.edu/cyber-security-programs/bachelors-degree/
———–
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.