-
Analyzing “Zombie Zip” Files (CVE-2026-0866), (Wed, Mar 11th)
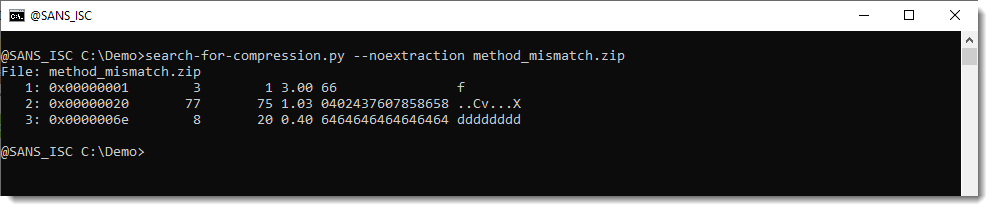
A new vulnerability (CVE-2026-0866) has been published: Zombie Zip. It’s a method to create a malformed ZIP file that will bypass detection by most anti-virus engines. The malformed ZIP file can not be opened with a ZIP utility, a custom loader is required. The trick is to change the compression method to STORED while the contend…
-
ISC Stormcast For Wednesday, March 11th, 2026 https://isc.sans.edu/podcastdetail/9844, (Wed, Mar 11th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
Microsoft Patch Tuesday March 2026, (Tue, Mar 10th)
Microsoft today released patches for 93 vulnerabilities, including 9 vulnerabilities in Chromium affecting Microsoft Edge. 8 of the vulnerabilities are rated critical. 2 were disclosed prior to today but have not yet been exploited. This update addresses no already-exploited vulnerabilities. Disclose vulnerabilities: CVE-2026-26127: A denial of service vulnerability in .Net. Microsoft considers exploitation unlikely. The…
-
ISC Stormcast For Tuesday, March 10th, 2026 https://isc.sans.edu/podcastdetail/9842, (Tue, Mar 10th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
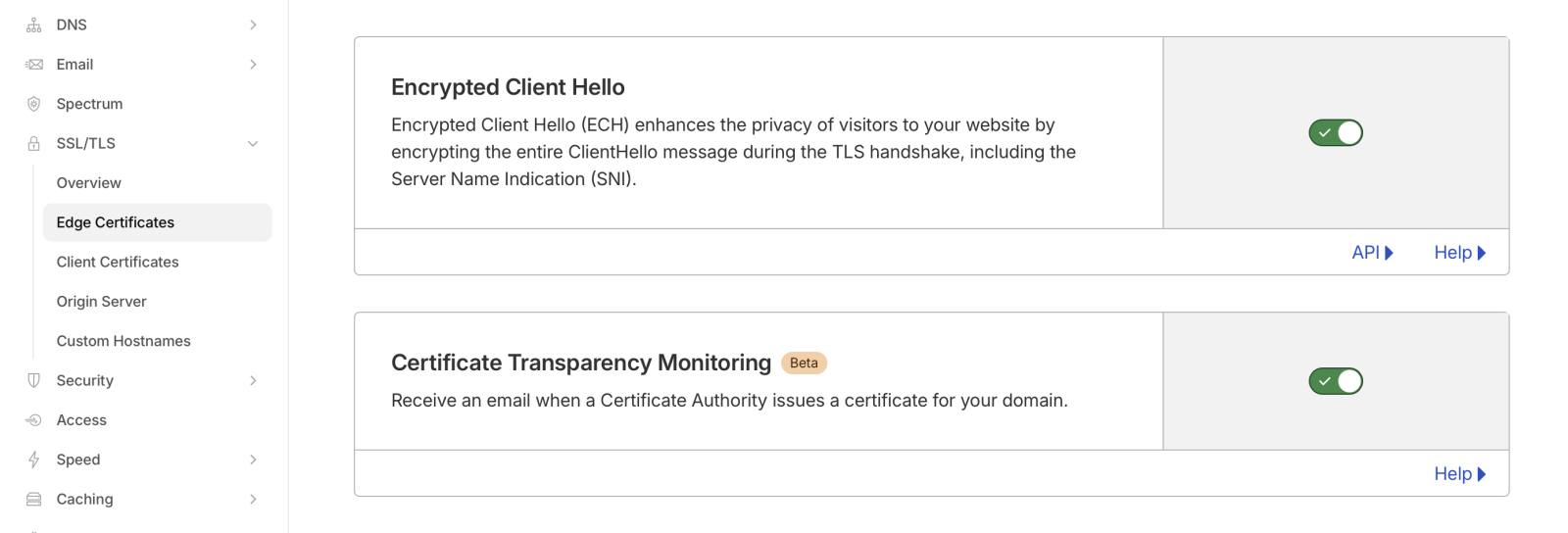
Encrypted Client Hello: Ready for Prime Time?, (Mon, Mar 9th)
Last week, two related RFCs were published: RFC 9848: Bootstrapping TLS Encrypted ClientHello with DNS Service Bindings RFC 9849: TLS Encrypted Client Hello These TLS extensions have been discussed quite a bit already, and Cloudflare, one of the early implementers and proponents, has been in use for a while. Amidst an increased concern about threats to privacy…
-
ISC Stormcast For Monday, March 9th, 2026 https://isc.sans.edu/podcastdetail/9840, (Mon, Mar 9th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
YARA-X 1.14.0 Release, (Sat, Mar 7th)
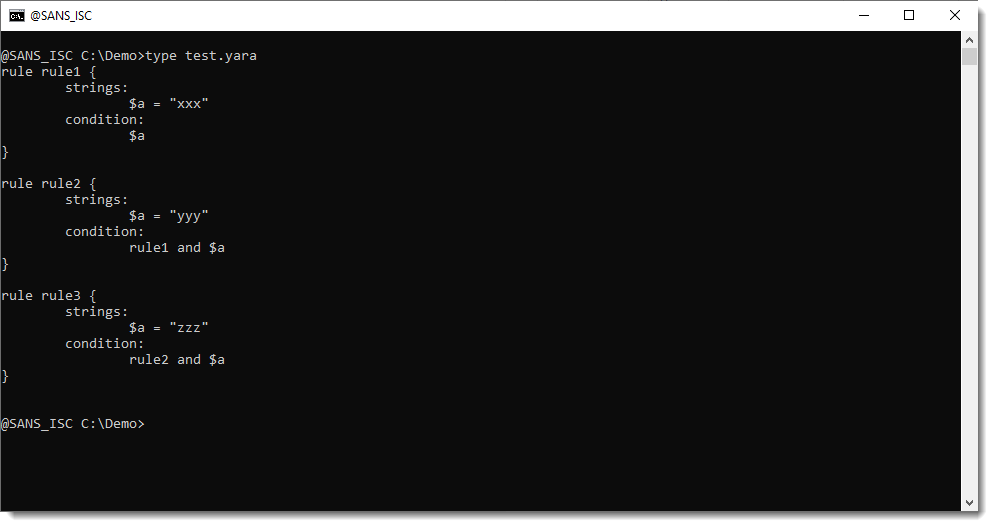
YARA-X’s 1.14.0 release brings 4 improvements and 2 bugfixes. One of the improvements is a new CLI command: deps. This command shows you the dependencies of rules. Here is an example. Rule rule1 has no dependencies, rule rule2 depends on rule rule1 and rule rule3 depends on rule rule2: Running the deps command on these rules…
-
ISC Stormcast For Friday, March 6th, 2026 https://isc.sans.edu/podcastdetail/9838, (Fri, Mar 6th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
ISC Stormcast For Thursday, March 5th, 2026 https://isc.sans.edu/podcastdetail/9836, (Thu, Mar 5th)
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.
-
![Differentiating Between a Targeted Intrusion and an Automated Opportunistic Scanning [Guest Diary], (Wed, Mar 4th)](/wp-content/uploads/2026/03/Joseph_Gruen_Picture1-hmhPDl.png)
Differentiating Between a Targeted Intrusion and an Automated Opportunistic Scanning [Guest Diary], (Wed, Mar 4th)
[This is a Guest Diary by Joseph Gruen, an ISC intern as part of the SANS.edu BACS program] The internet is under constant, automated siege. Every publicly reachable IP address is probed continuously by bots and scanners hunting for anything that can be exploited or retrieved. It’s not because there is a specific target, but…

